Why Your Cloud Service Needs a Clear Path Through FedRAMP Certification
Picture this: Your cloud solution has transformed commercial enterprises, earned stellar reviews, and captured significant market share. Federal agencies need exactly what you’ve built. Yet, without FedRAMP Certification, that rapidly growing federal cloud market — projected to exceed $30 billion by 2028 — remains completely out of reach. Even more concerning, the certification process — which can consume 12–18 months and hundreds of thousands of dollars — creates a barrier that stops innovative cloud providers before they even begin.
Understanding the FedRAMP Certification journey isn’t just about checking compliance boxes. Rather, it represents the difference between watching federal opportunities pass by and securing contracts that validate your security posture to government and commercial clients alike.
At databrackets, we’ve observed cloud service providers (CSPs) navigate this complex landscape. Through these experiences, we’ve identified obstacles that derail certification efforts and developed solutions to help organizations overcome them. This roadmap will guide you through each critical phase, ensuring your journey toward FedRAMP Certification moves forward with clarity and confidence.
Understanding the Strategic Value of FedRAMP Certification
Federal agencies aren’t just customers — they’re validators. Achieving FedRAMP Certification signals to the entire market that your security controls meet the federal government’s most stringent requirements. This certification opens doors beyond government contracts, as commercial enterprises increasingly seek cloud providers that demonstrate this level of security maturity.
The Federal Risk and Authorization Management Program (FedRAMP) standardizes security assessment, authorization, and continuous monitoring of cloud services. Consequently, federal agencies can adopt secure cloud solutions without conducting redundant security reviews for each vendor. Meanwhile, cloud providers gain access to a marketplace where their certification becomes reusable across multiple agencies.
Recent program updates have introduced pathways designed to reduce barriers while maintaining security rigor. The FedRAMP 20x initiative, for instance, emphasizes automation and continuous monitoring over traditional documentation-heavy processes. Additionally, the streamlined approach eliminates the Joint Authorization Board (JAB) P-ATO path entirely in favor of a single Agency ATO designation — governed by the FedRAMP Board established under OMB Memorandum M-24-15 — creating a more scalable and consistent framework for bringing innovative cloud services to federal agencies.
Important FedRAMP Terminology Update (February 2026)
FedRAMP has officially adopted new terminology based on the FedRAMP Authorization Act and public comment outcomes from RFC-0020. The single official label for all FedRAMP authorizations is now FedRAMP Certification or FedRAMP Certified. The output of the process is called a FedRAMP Certification Package. These terms replace earlier references to “FedRAMP Authorization” and “ATO” at the program level, though individual agencies still issue their own Authority to Operate (ATO) letters. This terminology is in effect now and will be formally codified in the FedRAMP Consolidated Rules for 2026 (CR26), expected by the end of June 2026.
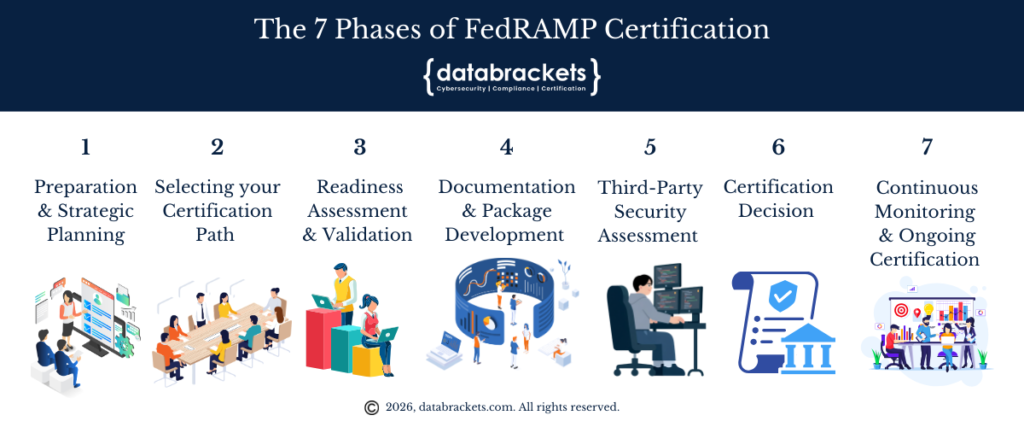
The 7 Phases of FedRAMP Certification
The FedRAMP Certification journey unfolds across seven distinct phases, each building on the last. While no two organizations move through this process identically, understanding what lies ahead enables smarter planning, better resource allocation, and fewer surprises along the way.
Phase 1 — Preparation and Strategic Planning establishes your security foundation before formal engagement with the FedRAMP PMO begins. This phase involves defining your authorization boundary, implementing NIST SP 800-53 controls, and developing your System Security Plan (SSP). Organizations that invest meaningfully in this phase consistently experience smoother assessments downstream.
Phase 2 — Selecting Your Certification Path involves securing a federal agency sponsor and formally initiating your relationship with the FedRAMP PMO through an In Process Request. The sponsoring agency becomes your advocate throughout the process, helping navigate requirements and aligning your cloud service offering with their mission needs.
Phase 3 — Readiness Assessment and Validation provides an objective, independent evaluation of your security posture before you commit fully to the certification process. A 3PAO-conducted Readiness Assessment identifies gaps early, informs your timeline and budget, and gives potential agency sponsors confidence in your readiness.
Phase 4 — Documentation and Package Development transforms your security implementation into a comprehensive certification package. This resource-intensive phase requires technical accuracy, narrative coherence, and strict adherence to FedRAMP-provided templates. Documentation quality here directly determines how efficiently your package moves through review.
Phase 5 — Third-Party Security Assessment puts your controls to the test. Your 3PAO evaluates your security posture through interviews, technical testing, vulnerability scanning, and documentation review — ultimately producing a Security Assessment Report (SAR) that becomes the centerpiece of your certification package.
Phase 6 — Certification Decision places your package before your sponsoring agency’s authorizing official for a risk-based review. This phase concludes with the issuance of an Authority to Operate (ATO), granting your cloud service permission to process federal data and establishing your presence in the FedRAMP Marketplace with an official FedRAMP Certification.
Phase 7 — Continuous Monitoring and Ongoing Certification marks the beginning of your long-term certification obligations. Monthly vulnerability scans, continuous monitoring reports, annual 3PAO assessments, and POA&M management ensure your security posture remains strong — and your certification remains valid — as your environment evolves.
Each of these phases is explored in detail in the sections that follow.
Phase 1: Preparation and Strategic Planning
Successful FedRAMP Certification begins long before your first interaction with the FedRAMP Program Management Office (PMO). Organizations that invest adequate time in preparation consistently move through the certification process more efficiently than those rushing into documentation without foundational readiness.
1.1 Defining Your Authorization Boundary
Your authorization boundary establishes exactly what components, data flows, and services fall within the scope of FedRAMP Certification. This foundational element appears in every subsequent document and undergoes validation during the Third-Party Assessment Organization (3PAO) assessment.
Poorly defined boundaries represent one of the most common obstacles encountered during certification. Specifically, CSPs often fail to accurately depict data flow diagrams or exclude external services where federal data passes through systems not yet certified. Furthermore, dependencies on services authorized at a lower certification class than your target create complications requiring resolution before proceeding.
Best practices include creating comprehensive architecture diagrams that show all system components, identifying every point where data enters or exits your environment, and ensuring any external services touching federal data already possess appropriate FedRAMP Certification.
1.2 Building Your Security Foundation
FedRAMP Certification requires demonstrating that your cloud service implements security controls aligned with NIST SP 800-53 standards. Organizations with mature security practices before starting the process move through assessments more smoothly than those building controls reactively.
Controls span multiple domains including access management, incident response, encryption, configuration management, and continuous monitoring. Although the volume of requirements can feel overwhelming, systematic implementation following established frameworks creates a solid foundation for certification success.
Investment in proper resources pays dividends throughout the journey. Organizations lacking experienced technical writers with security expertise should consider engaging advisory partners who understand both FedRAMP requirements and how to articulate security implementations effectively. Many FedRAMP-recognized 3PAOs offer advisory services in addition to assessment capabilities, though CSPs must engage different organizations for advisory and assessment roles to maintain independence.
1.3 Developing Your System Security Plan
The System Security Plan (SSP) stands as the cornerstone document for FedRAMP Certification. This comprehensive artifact details how your organization addresses each relevant security control and manages configuration processes across your cloud environment.
Quality matters tremendously. A well-crafted SSP demonstrates clear alignment between your security implementation and federal requirements, whereas poorly written, incomplete, or inconsistent documentation creates delays and requires extensive remediation. Documentation quality represents a primary barrier to certification success.
Your SSP should include detailed system overviews with architecture diagrams, security requirements mapping demonstrating NIST 800-53 alignment, configuration management processes showing how changes occur without introducing security risks, and customer responsibility matrices clarifying which controls agencies must implement themselves.
Phase 2: Selecting Your Certification Path
FedRAMP Certification now follows a streamlined agency-driven pathway following the 2024 program modernization. Understanding how this path works helps CSPs align their strategy with PMO expectations and federal agency needs.
2.1 Agency Sponsorship Strategy
Most organizations pursuing FedRAMP Certification begin by identifying a federal agency willing to sponsor their certification. This partnership proves essential because agencies understand their own risk tolerance, mission requirements, and how your cloud service supports their objectives.
Common misconceptions suggest agencies reluctantly sponsor certifications. However, federal organizations actively seek cloud providers that help them achieve mission goals while meeting security requirements. They recognize cloud computing’s benefits — remote access, scalability, collaboration efficiency — and want to leverage these capabilities.
Successful sponsorship strategies involve demonstrating clear value propositions aligned with agency missions, showing strong existing commercial track records that validate your technology, and articulating realistic timelines based on your current security posture.
Understanding What FedRAMP Certification Means for Agencies
An important clarification from FedRAMP’s February 2026 notice: a FedRAMP Certification is not a guarantee that a cloud service is pre-approved for use at a specific FIPS 199 security category. It is a package of reusable materials that enables agencies to make their own risk-based decisions efficiently. Agencies may use a FedRAMP Certification Package to authorize a cloud service at a different security category than the certification class itself, following the Risk Management Framework. This distinction matters when setting expectations with prospective agency sponsors.
2.2 Engaging the FedRAMP PMO
After securing agency sponsorship, CSPs submit an In Process Request to the FedRAMP PMO along with a Work Breakdown Structure showing project timelines. This formal initiation marks your entry into the FedRAMP certification process.
The PMO conducts an intake call to review your submission and provide guidance on next steps. Subsequently, they schedule a Kickoff Meeting where key stakeholders meet to review your cloud service offering and align on the overall certification process.
During this kickoff, participants establish shared understanding regarding certification milestones, deliverables, roles, responsibilities, and schedules. Additionally, discussions cover your service’s purpose and function, authorization boundary, data flows, known security gaps with remediation plans, agency-specific requirements, and customer-responsible controls.
Phase 3: Readiness Assessment and Validation
Although not strictly mandatory, a formal Readiness Assessment Report (RAR) conducted by a 3PAO provides substantial value early in the FedRAMP Certification journey. This assessment evaluates whether your organization stands prepared to begin the formal certification process.
3.1 Benefits of Readiness Assessment
Organizations conducting readiness assessments identify gaps in their security posture before investing fully in certification documentation. Consequently, they can address deficiencies proactively rather than discovering issues during the formal security assessment.
The readiness assessment provides objective validation from an independent security assessor. This external perspective often reveals blind spots internal teams miss and offers recommendations grounded in experience helping other CSPs achieve FedRAMP Certification.
Furthermore, readiness assessment findings inform your certification timeline and budget more accurately. Understanding the scope of work remaining helps you allocate resources effectively and set realistic expectations with agency sponsors and internal stakeholders.
3.2 Selecting Your 3PAO Partner
3PAOs play a critical role in the FedRAMP Certification journey. These FedRAMP-accredited organizations conduct independent security assessments ensuring cloud services meet federal security standards.
Choosing the right 3PAO partner significantly impacts your certification experience. Qualified assessors guide CSPs through complexities, help correct issues before final submission, and bring expertise from working with multiple organizations through the certification process.
To be FedRAMP-recognized, 3PAOs must be accredited by the American Association for Laboratory Accreditation (A2LA) and meet ISO/IEC 17020 requirements. You can verify any prospective assessor’s current status on the FedRAMP Marketplace before engaging. Beyond accreditation, evaluation criteria should include the assessor’s experience with your service model (SaaS, PaaS, or IaaS), their track record of successful certifications, communication practices and responsiveness, and technical depth across security domains relevant to your implementation.
Phase 4: Documentation and Package Development
Creating comprehensive security documentation represents one of the most resource-intensive aspects of FedRAMP Certification. Organizations must produce thousands of pages demonstrating how they implement, monitor, and maintain security controls.
4.1 Documentation Best Practices
Template adherence proves essential. The FedRAMP PMO provides standardized templates that must be used for all certification packages. These templates ensure consistency across certifications and enable efficient review processes.
Narrative quality distinguishes successful packages from those requiring extensive revision. Security documentation should tell a coherent story about how your organization protects federal data. When gaps exist in this narrative, reviewers require you to address inconsistencies before certification proceeds.
Technical accuracy cannot be compromised. Documentation must accurately reflect your actual security implementation rather than aspirational goals. Assessors will validate claims through testing, and discrepancies between documentation and reality create significant delays.
4.2 Required Documentation Components
FedRAMP Certification packages include multiple interconnected documents. The SSP serves as the primary artifact, supplemented by configuration baseline documentation showing system hardening standards, incident response plans detailing how you detect and respond to security events, and continuous monitoring strategies explaining ongoing security validation.
Organizations must also prepare security policies governing how employees and systems interact with federal data, procedures translating policies into actionable steps, and evidence artifacts demonstrating control implementation through screenshots, logs, and configuration exports.
Phase 5: Third-Party Security Assessment
The 3PAO assessment represents a comprehensive evaluation of your security posture. During this phase, assessors test whether your implemented controls actually function as documented and meet FedRAMP Certification requirements.
5.1 Assessment Methodology
Assessors evaluate security controls through multiple techniques. Interviews with technical staff verify understanding of security requirements and implementation approaches. Documentation reviews ensure policies and procedures align with NIST 800-53 control families.
Technical testing validates that controls operate effectively. For instance, assessors attempt to access systems without proper authorization, verify encryption implementations protect data in transit and at rest, and confirm logging captures security-relevant events adequately.
Vulnerability scanning identifies weaknesses in your environment that require remediation before FedRAMP Certification can proceed. While some findings fall within acceptable risk parameters, others demand correction prior to certification.
5.2 Security Assessment Report
Upon completing their evaluation, the 3PAO produces a Security Assessment Report (SAR) detailing findings and including a recommendation regarding FedRAMP Certification. This document becomes a critical component of your certification package.
The SAR categorizes findings by severity and maps them to specific NIST 800-53 controls. Organizations must address these findings through their Plan of Action and Milestones (POA&M), which outlines remediation strategies and timelines.
Working collaboratively with your 3PAO during SAR development helps ensure findings accurately reflect your environment and that proposed remediation approaches align with FedRAMP expectations. Subsequently, you’ll present SAR results during a debrief meeting attended by your agency sponsor and the FedRAMP PMO.
Phase 6: Certification Decision
After completing documentation and assessment activities, the FedRAMP Certification package undergoes review by your sponsoring agency’s authorizing official. This phase determines whether your cloud service receives permission to process federal data.
6.1 Risk-Based Decision Framework
Federal authorizing officials evaluate FedRAMP Certification requests through a risk management lens. They consider the SAR findings in context of your organization’s POA&M, the sensitivity of data your service will process, and how your service supports their agency’s mission objectives.
Agencies don’t expect perfection. Rather, they seek assurance that you’ve implemented appropriate controls, you understand residual risks and have plans for mitigation, and your organization demonstrates commitment to maintaining security over time.
It is equally important to understand what a FedRAMP Certification does not represent. Per FedRAMP’s official guidance, a FedRAMP Certification is not a determination that a cloud service is automatically appropriate for use at a given FIPS 199 security category. FedRAMP does not have the authority to make that determination on behalf of an agency’s authorizing official. Agencies use the FedRAMP Certification Package as a foundation for their own risk-based decision-making and may authorize a service at a security category different from the certification class itself. This distinction matters for how you present your certification credentials to prospective agency customers.
Communication during this phase helps address questions and concerns proactively. Authorizing officials may request additional information or clarification on specific findings before rendering their decision.
6.2 Authority to Operate (ATO) and FedRAMP Certification
Successful completion of the process culminates in two distinct but related outcomes. First, your sponsoring agency issues an Authority to Operate (ATO) letter, formally permitting your cloud service to process federal data for that agency. Second — and at the program level — FedRAMP records your status as FedRAMP Certified, and your listing appears in the FedRAMP Marketplace as a FedRAMP Certification Package.
Marketplace presence creates reusability opportunities. Other federal agencies can leverage your FedRAMP Certification Package when conducting their own risk assessments, significantly reducing the time and resources required for them to adopt your service.
Phase 7: Continuous Monitoring and Ongoing Certification
Receiving your initial FedRAMP Certification represents a beginning rather than an endpoint. Maintaining certification requires ongoing security monitoring and regular reporting to demonstrate continued compliance.
7.1 Monthly Continuous Monitoring
Organizations with FedRAMP Certification must conduct monthly vulnerability scanning and deliver continuous monitoring reports to their agency partners and the FedRAMP PMO. These reports provide visibility into your security posture evolution over time.
Continuous monitoring reports document new vulnerabilities discovered since the previous month, remediation progress on existing POA&M items, configuration changes that could impact your security baseline, and incidents or events requiring attention.
Timely, accurate reporting builds trust with federal partners and demonstrates your commitment to maintaining the security standards that earned initial certification.
7.2 Annual Assessment Requirements
Beyond monthly monitoring, certified organizations undergo annual security assessments conducted by their 3PAO. These assessments verify that security controls continue operating effectively and that your organization maintains compliance as your environment evolves.
Annual assessments follow methodologies similar to the initial certification but typically focus on areas where changes have occurred or where previous findings warranted additional scrutiny. Consequently, they generally require less time than the comprehensive initial assessment.
FedRAMP 20x and the New Certification Framework: What CSPs Need to Know Now
The FedRAMP 20x initiative, combined with the new FedRAMP Certification framework announced in February 2026, represents a fundamental shift in how FedRAMP operates. Understanding these changes — particularly the new Certification Classes, the upcoming Consolidated Rules, and the phased rollout of 20x — is essential for any CSP planning their certification strategy today.
New Certification Classes Replace Low/Moderate/High Impact Level Labels
As announced in FedRAMP Notice NTC-0004 (February 25, 2026), FedRAMP is replacing the traditional Low, Moderate, and High impact level labels for assessment baselines with a new FedRAMP Certification Class system. The new labels deliberately avoid the terms “levels” or numbers to prevent confusion with the Department of Defense Impact Level (IL) system. Instead, baselines will be identified by class:
Class A — A new pilot baseline (Rev5)
Class B — Encompasses the current Li-SaaS and Low baselines (Rev5)
Class C — Encompasses the current Moderate baseline (Rev5)
Class D — Encompasses the current High baseline (Rev5)
Importantly, these new class labels reflect the scope of the assessment and the depth of information provided — not a ranking of the overall quality or security of a cloud service. The FedRAMP 20x path will align with these same Rev5 classes as it matures. There will be a transition period during which old and new labels will be linked, with full details provided in the Consolidated Rules for 2026.
One Designation for All Paths: No Separate Labels for 20x and Rev5
A notable outcome from the RFC-0020 public comment process: FedRAMP will not create separate designations for 20x and Rev5 authorization paths. Earlier proposals had considered labels such as “FedRAMP Validated” to distinguish 20x from Rev5 certifications. This approach was rejected based on commenter feedback that separate labels would create confusion in procurement conversations.
Both 20x and Rev5 paths lead to the same FedRAMP Certification designation. Marketplace filters — not separate labels — will allow agencies and procurement teams to differentiate between the two paths. For CSPs, this means a 20x Certification carries identical standing to a Rev5 Certification in federal procurement contexts.
Automation and Continuous Validation
Traditional FedRAMP Certification relied heavily on point-in-time assessments and manual documentation review. FedRAMP 20x is actively changing this approach across two pilot phases. Phase 1, which tested automation-based Low impact certifications, concluded in late 2025 with 12 initial 20x Low pilot certifications. Phase 2, focused on extending the 20x model to Moderate certifications, is currently underway with 13 selected pilot participants and is expected to conclude by March 31, 2026. Wide-scale adoption of 20x Low and Moderate paths is currently projected for Q3–Q4 of FY2026.
Cloud providers participating in 20x pilots generate structured outputs — including OSCAL-formatted files, JSON data, and API feeds — that provide ongoing, automated visibility into security posture. This approach enables continuous control monitoring while substantially reducing the documentation burden of traditional Rev5 authorization.
Organizations building toward FedRAMP Certification should consider how automation can strengthen their security programs. Tools enabling continuous compliance monitoring position you advantageously as the program evolves — and as FedRAMP’s long-term roadmap moves toward requiring all Rev5 authorized providers to transition to machine-readable authorization data.
Decentralized Compliance Interactions
Under FedRAMP 20x, compliance responsibilities shift from centralized PMO review toward direct engagement between CSPs and federal agencies. This decentralization requires greater autonomy and maturity from cloud providers.
Organizations pursuing FedRAMP Certification must prepare to maintain real-time compliance dashboards, conduct internal risk assessments and control validation independently, and work directly with agency sponsors to address security changes or incidents.
FedRAMP Consolidated Rules for 2026 (CR26): What CSPs Need to Plan For Now
FedRAMP will publish the FedRAMP Consolidated Rules for 2026 (CR26) by the end of June 2026. These rules will be valid through December 31, 2028. CR26 will formally codify the new FedRAMP Certification terminology, the Class A–D baseline labels, the 20x requirements formalized from pilot phases, and any updates stemming from the RFC-0020 outcomes. CSPs beginning their certification journey today should expect that CR26 — not current legacy guidance alone — will govern key aspects of their process. Align your planning horizon accordingly.
Common Obstacles and Solutions
Through our work supporting organizations seeking FedRAMP Certification, we’ve identified recurring challenges and effective approaches for overcoming them.
1. Resource and Timeline Management
FedRAMP Certification demands significant investment in people, processes, and technology. Organizations frequently underestimate the effort required, leading to timeline slips and budget overruns.
Solutions include building cross-functional teams combining security, compliance, engineering, and documentation expertise. Additionally, realistic timeline planning accounting for the 12–18-month average certification duration helps set appropriate expectations. Phased resource allocation proves effective: organizations can ramp up documentation efforts once they’ve completed readiness assessment rather than staffing fully from day one.
2. Technical Complexity
The sheer volume of NIST 800-53 controls spanning access management, incident response, encryption, and numerous other domains can overwhelm even experienced security teams. Structured implementation roadmaps help manage this complexity by breaking requirements into manageable components. Organizations should prioritize controls based on their current security posture, focusing first on areas requiring the most development.
Leveraging inheritable controls from certified infrastructure providers significantly reduces the control burden. CSPs building on FedRAMP-certified platforms can inherit numerous infrastructure-layer controls, allowing them to focus on application and data-layer security.
3. Vendor Dependency Challenges
FedRAMP Certification requires that all external services processing or storing federal data hold appropriate certification at or above your target class. Organizations frequently discover vendor dependency gaps during certification that require addressing. Proactive vendor assessment identifies these gaps early. Review all services in your architecture, determine which handle federal data, and verify their FedRAMP Certification status before beginning your certification journey.
For critical vendors lacking certification, you face choices: find FedRAMP-certified alternatives, sponsor your vendor through their own certification process (resource-intensive), or architect federal data flows to avoid the uncertified service entirely.
Strategic Recommendations for FedRAMP Certification Success
Organizations embarking on the FedRAMP Certification journey benefit from strategic approaches grounded in lessons learned from successful certifications.
1. Invest in Preparation
Organizations that invest adequate time preparing their security foundation before initiating formal FedRAMP Certification consistently experience smoother processes. This preparation includes implementing robust security controls, developing comprehensive documentation practices, and building organizational security culture. Early engagement with potential 3PAO partners provides valuable perspective on your readiness. Many assessors offer pre-engagement consultations helping organizations understand their current maturity level.
2. Prioritize Clear Communication
Transparent, frequent communication with all stakeholders — agency sponsors, the FedRAMP PMO, your 3PAO, and internal teams — prevents misunderstandings and keeps certification efforts on track. Weekly status meetings provide forums for addressing questions, escalating issues, and maintaining alignment on deliverables and timelines. Documentation of decisions made during these meetings creates shared understanding and accountability.
3. Embrace Continuous Improvement
FedRAMP Certification should catalyze security program maturation rather than represent a mere compliance exercise. Organizations that view certification as an opportunity to strengthen their security posture develop more robust programs benefiting all customers. Regular internal security reviews beyond FedRAMP requirements help identify opportunities for improvement. Participation in security communities and working groups exposes you to evolving best practices.
Moving Forward on Your FedRAMP Certification Journey
The path to FedRAMP Certification requires commitment, resources, and expertise. Organizations that approach the journey strategically — understanding requirements, preparing thoroughly, and engaging the right partners — successfully achieve certification and unlock federal market opportunities. The organizations that succeed in the federal cloud market aren’t the ones who move fastest — they’re the ones who prepare most deliberately. This roadmap gives you the framework to do exactly that.
Key Takeaways
Start with security, not paperwork. FedRAMP Certification is built on a foundation of genuinely implemented controls, not well-written documentation. If your security program isn’t mature, no amount of polished narrative will accelerate your certification. Strengthen your controls first — the documentation will follow naturally.
Your authorization boundary defines everything that comes after it. Get this wrong and every downstream document, diagram, and assessment inherits that error. Before writing a single page of your SSP, invest serious time mapping your architecture, data flows, and external dependencies with precision.
Treat the seven-phase structure as your operational map, not background reading. Each phase has distinct deliverables, decision points, and dependencies. CSPs who familiarize themselves with this structure early can anticipate what’s coming, allocate resources at the right moments, and avoid the costly mistake of treating later phases as distant problems.
An agency sponsor is a partner, not a formality. The right sponsoring agency understands your technology, believes in its mission value, and actively supports your certification journey. Approach sponsorship as a relationship you’re building — not a signature you’re collecting.
Budget for the full journey, not just the assessment. The 3PAO assessment is one phase in a multi-phase commitment. Organizations that underfund preparation and documentation often spend more correcting avoidable deficiencies than they would have investing upfront. Plan your resources across all seven phases from day one.
Independence in your 3PAO relationship isn’t optional — it’s structural. If you’re working with a 3PAO for advisory support, that organization cannot also serve as your assessor. Understand this early and structure your partnerships accordingly to avoid delays caused by independence conflicts.
Certification is a milestone. Continuous monitoring is the mission. Receiving your FedRAMP Certification opens the federal market — but failing to maintain rigorous monthly monitoring, timely POA&M remediation, and annual assessments can unravel that certification. Build your ConMon capabilities before you need them.
FedRAMP 20x and CR26 are present-day design considerations, not future concerns. If you’re beginning your certification journey now, architect your systems and compliance programs with automation and machine-readable outputs in mind. Understand the new Certification Class framework and anticipate that the FedRAMP Consolidated Rules for 2026 (CR26) — expected by June 2026 — will govern your process. Organizations that wait to adapt will face costly rework as the program evolves.
Summary
FedRAMP Certification is not a compliance checkbox — it’s a strategic gateway to the multi-billion-dollar federal cloud market and a signal of security maturity that resonates well beyond government contracts.
The journey moves through seven structured phases: building your security foundation, securing agency sponsorship, validating readiness, developing documentation, completing your 3PAO assessment, receiving your FedRAMP Certification, and sustaining it through continuous monitoring. Each phase depends on the one before it. Rushing ahead without adequate preparation consistently extends timelines and inflates costs.
Several factors determine how smoothly organizations move through this process: the maturity of existing security controls, the quality of documentation, the experience of your 3PAO partner, and the clarity of your authorization boundary. Organizations that treat FedRAMP Certification as a security program investment — rather than a documentation exercise — achieve certification faster and maintain it with less friction.
Two significant structural changes are reshaping the landscape for CSPs starting their journey today. First, FedRAMP has introduced a new Certification Class framework (Classes A through D), replacing the Low/Moderate/High labeling system, with both 20x and Rev5 paths leading to the same FedRAMP Certification designation. Second, the FedRAMP Consolidated Rules for 2026 (CR26) will be published by end of June 2026, formally codifying these changes through December 31, 2028. Cloud providers building toward certification now should align their security programs with this direction from the outset.
How databrackets can help you with your FedRAMP Journey
databrackets is an A2LA-accredited 3PAO and FedRAMP advisory organization. We offer 3PAO Assessment Services OR Advisory Services for FedRAMP. To avoid a conflict of interest and abide by FedRAMP’s independence requirements, we do not offer both services to the same client.
We are an ideal partner for either service since we bring over 15 years of proven expertise in helping organizations achieve compliance or certification with the most rigorous cybersecurity and data privacy standards, including NIST SP 800-53, NIST SP 800-171, NIST Cybersecurity Framework, ISO 27001, SOC 2, CMMC, HIPAA, and GDPR. We are an authorized certifying body for ISO 27001 and authorized C3PAO for CMMC.
Schedule a meeting to work with us as your 3PAO for FedRAMP Assessment or as your Advisory Partner to help you prepare for it.
A. Why Choose databrackets as Your FedRAMP 3PAO
As an A2LA-accredited 3PAO listed on the FedRAMP Marketplace, databrackets conducts the independent security assessments that federal agencies and the FedRAMP PMO rely on for certification decisions. Our assessment services are structured to give your certification package the rigor, accuracy, and credibility it needs to move efficiently through agency review.
1. Assessment-Informed Perspective
Our 3PAO teams bring direct experience conducting assessments across Certification Classes A through D — spanning the full range from Low through High Impact level complexity. We understand how federal reviewers evaluate certification packages, where documentation gaps create delays, and what assessors test for in each control family. This translates into a more focused, efficient assessment experience for your team.
2. Proven Multi-Framework Expertise
What makes databrackets particularly valuable is our experience across complementary frameworks including NIST SP 800-53, NIST SP 800-171, NIST Cybersecurity Framework, ISO 27001, SOC 2, CMMC, and HIPAA. This breadth of knowledge enables our assessment teams to understand how FedRAMP controls integrate with your existing compliance efforts and identify efficiencies that strengthen your overall security posture beyond simply meeting FedRAMP requirements.
3. Technical Environment Proficiency
Our assessment team has specialized technical competence across diverse environments — from traditional on-premises infrastructures to complex cloud deployments across SaaS, PaaS, and IaaS models. Whatever your architecture, our assessors understand how to evaluate it accurately and completely.
4. Strategic Timeline Management
We understand how to conduct comprehensive assessments without unnecessarily disrupting your operations. Before testing begins, we ensure your assessment is properly scoped and timed to your architecture and business timeline — avoiding the costly delays that poorly planned assessments create.
Our 3PAO Assessment Services include Mock Assessments, FedRAMP-compliant Penetration Testing, Initial Security Assessments, Certification Package support, and Continuous Monitoring and Annual Assessments.
To inquire about our 3PAO Assessment Services, contact our team at sales@databrackets.com or schedule a meeting.
B. Why Choose databrackets for Your FedRAMP Advisory Journey
We specialize in helping Cloud Service Providers navigate the FedRAMP Certification journey with clarity, efficiency, and a realistic understanding of what the process demands. Our advisory services are directly informed by our 3PAO assessment experience — we know what assessors look for and how you need to prepare for it.
1. Assessment-Informed Guidance
Because we conduct FedRAMP assessments as an accredited 3PAO, our advisory teams bring a unique vantage point to preparation work. We’ve seen the documentation gaps, boundary definition errors, and control implementation weaknesses that create findings and delay certifications. Our advisory clients benefit from that institutional knowledge before they sit across from an assessor.
2. Proven Multi-Framework Expertise
Our advisory teams are fluent across NIST SP 800-53, NIST SP 800-171, NIST Cybersecurity Framework, ISO 27001, SOC 2, CMMC, and HIPAA. For CSPs already operating within existing compliance programs, we identify control overlaps and implementation efficiencies that reduce the burden of building a FedRAMP security program from scratch.
3. Practical Implementation Focus
We don’t just explain what FedRAMP requires — we help you understand how to implement it in your specific cloud environment. From authorization boundary definition and SSP development to policy creation and continuous monitoring strategy, our guidance is designed to produce work product that withstands 3PAO scrutiny.
4. End-to-End Advisory Support
We support CSPs from initial gap analysis through post-certification continuous monitoring, ensuring you have the guidance you need at every stage of the advisory engagement — without the handoff gaps that occur when multiple unconnected vendors are involved.
Our FedRAMP Advisory Services include Gap Analysis, System Security Plan Development, Policy and Plan Development, Readiness Assessment Preparation, and Continuous Monitoring Advisory.
To inquire about our FedRAMP Advisory Services, contact our team at sales@databrackets.com or schedule a meeting.
Srini Kolathur
Srini is the Director of databrackets.com. He is a results-driven security and compliance professional with over 25 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are SOC 2, ISO 27001, CMMC, FedRAMP, NIST Security Standards, HIPAA, Security Risk Assessments, among others. His accreditations include Certified CMMC Assessor, CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE. He has verified all the technical information in this blog and co-authored it with Aditi Salhotra.