Cybersecurity Framework – SAMA
Saudi Arabian Monetary Authority is a Cybersecurity Framework to allow SAMA (“Member Organizations”) regulated financial institutions to identify and effectively manage cybersecurity threats. Member Organizations must implement the framework in order to ensure the protection of information assets and online services.
SAMA – The Need for Framework
According to a KPMG CEO Outlook study in 2020, 64 percent of CEOs in the Kingdom believe that protecting client data is crucial for the company to increase its customer base in the future. Up from 38 percent the previous year.
According to Forrester, 80% of current data breakings using privileged credentials reassure that the SAMA gives specific guidelines on Identity And Access Management (IAM) in Section 3.3 (Cyber Security Operations and Technology).
The SAMA Cyber Security Framework incorporates best practices from a variety of other government frameworks and industry standards, including the National Institute of Standards and Technology (NIST) Framework for Improving Critical Infrastructure Cybersecurity (NIST CSF), Payment Card Industry Data Security Standard (PCI DSS), ISO 27001/27002 Information Security Management Standards, Information Security Forum Standard of Good Practice for Information Security, Basel II International Convergence of Capital Measurement and Capital Standards.
The SAMA Cyber Security Framework is required for all banks, insurance firms, and financial organizations operating in Saudi Arabia.
SAMA – A Snapshot
In May 2017, the Saudi Arabian Monetary Authority (SAMA) established the SAMA Cyber Security Framework to increase resilience against cyber attacks.
This is consistent with a global trend in which government and banking industry regulators are adopting cybersecurity guidelines and recommendations. The updated European Payment Services Directive (PSD2), with its Strong Customer Authentication standards, is an excellent example. It has subsequently been a catalyst for safe Open Banking across the world, including in Bahrain.
SAMA created a cybersecurity framework (‘the Framework’) to identify appropriate measures to efficiently detect and resolve cybersecurity issues.
With the establishment of a Cybersecurity Framework, regulated companies are supported by the development of adequate cybersecurity governance, a robust infrastructure, and the investigative and preventative measures necessary.
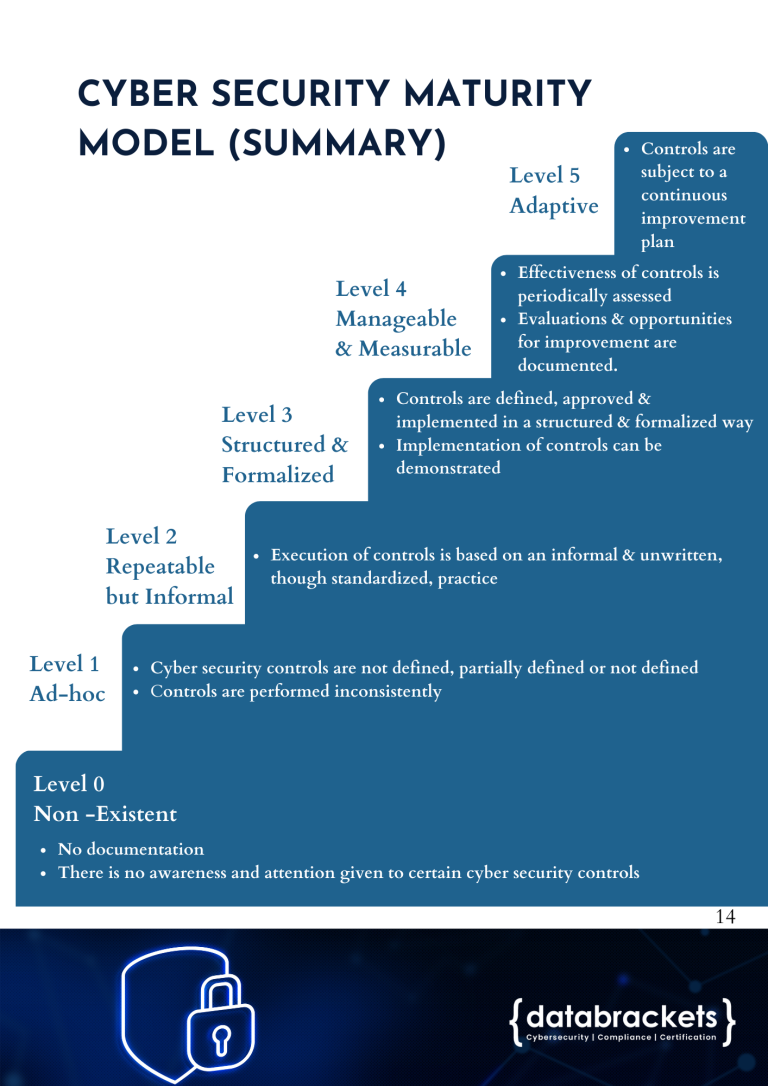
The Framework articulates relevant checks and gives direction on how maturity levels are evaluated. Adopting and implementing the Framework is a crucial step towards ensuring that Cybersecurity threats are managed by Saudi Arabian Banking, Insurance, and Financing Companies.
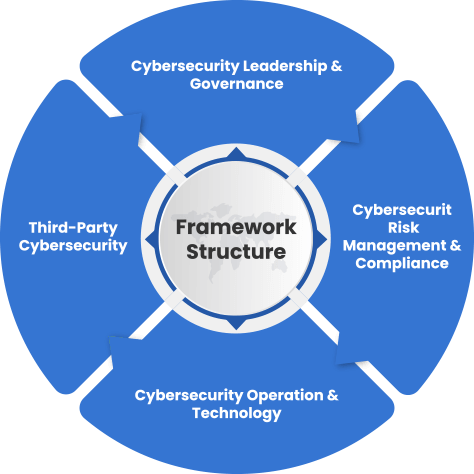
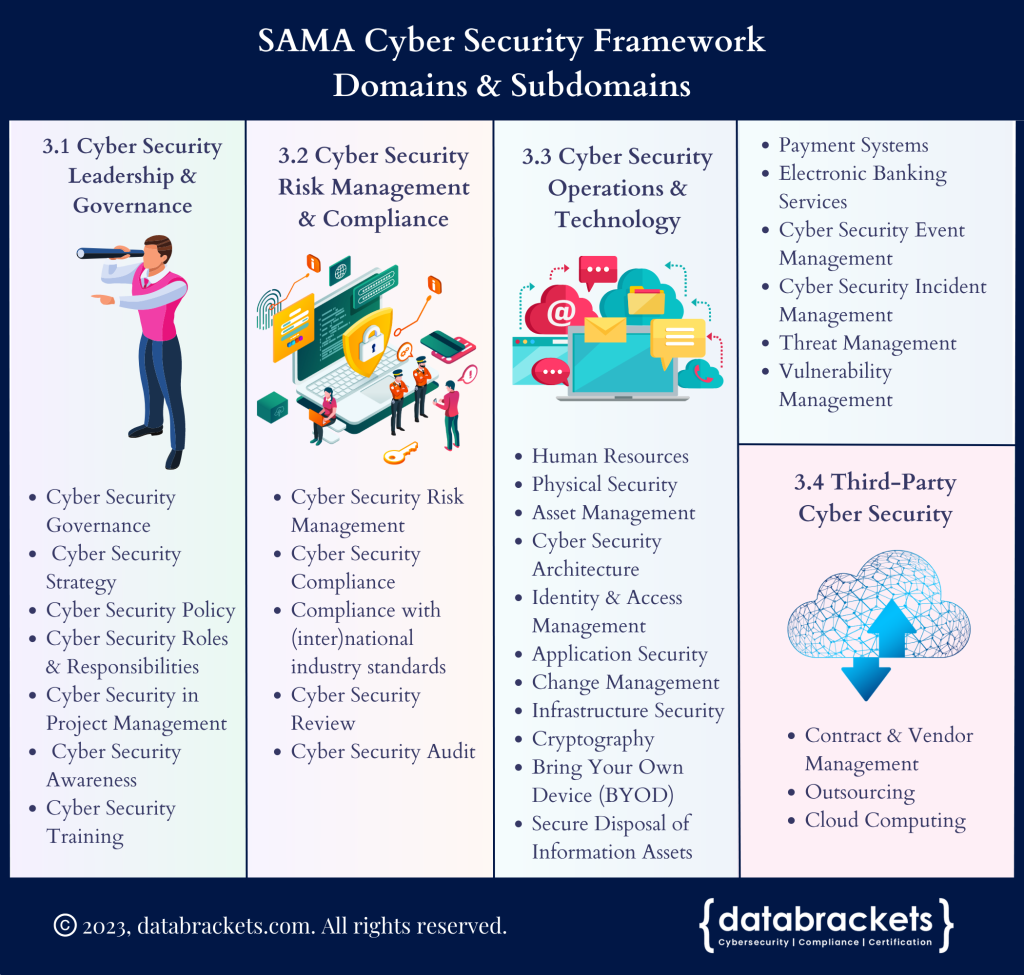
SAMA – Cybersecurity Framework
SAMA Cybersecurity Maturity Levels
Get SAMA eBook
Preparation for SAMA Compliance
Understand where data resides
Classify and get organized
Use the right tool
databrackets Online Portal
The Most Effective Cybersecurity Compliance Platform