Staffing Cybersecurity Job Roles
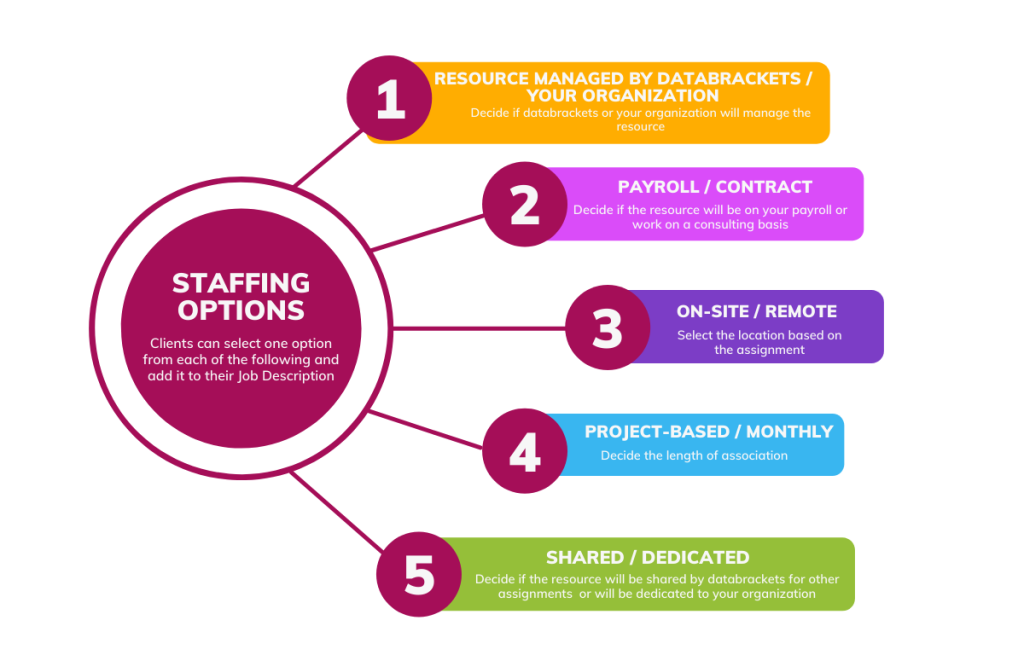
- Select the Job Title & Staffing option
- Select Full Time / Part Time Roles
- Recruit Cybersecurity Professionals on Payroll or Contract
As cyber threats and data breaches continue to evolve and become more sophisticated, it is essential for companies to build a strong cybersecurity team capable of safeguarding sensitive information and defending against potential attacks. At databrackets, we believe that investing in a robust cybersecurity workforce is not only a strategic advantage but also a necessity in today’s interconnected world.
In the course of delivering our services, we have worked with cyber security teams (in-house and outsourced) while supporting our clients to meet federal and global security benchmarks, receive certifications like ISO 27001 , comply with data privacy regulations like GDPR, HIPAA, SOC 2 etc. and maintain their Information Security Management Systems (ISMS). During these interactions, we have been asked countless times to help them find, replace and grow their teams. Our staffing services are a response to these requests, consisting of a series of staffing options, types of engagements and job titles you can choose from.
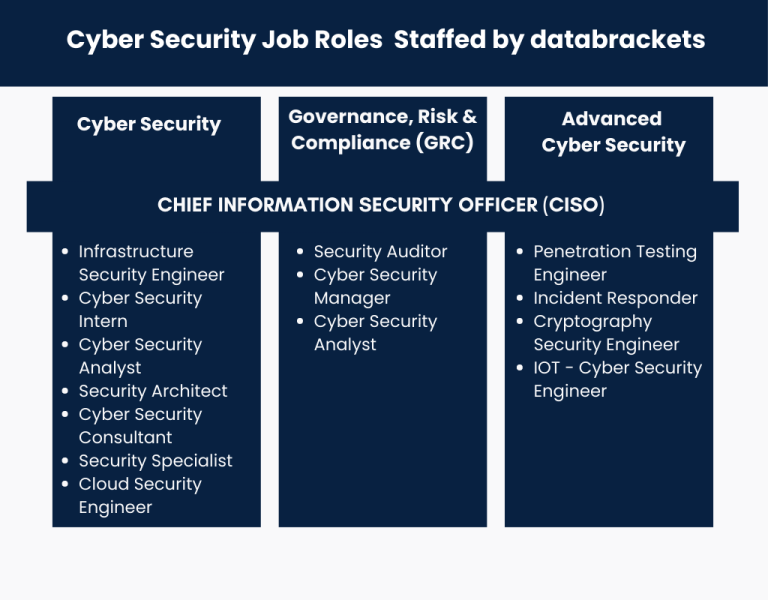
Select the Job Role(s)
Select the Staffing Option
Select the Location
- USA
- India
Trusted by Reputed Companies
What Our Clients Say
We used databrackets (formerly EHR 2.0) in our small medical practice for our risk analysis assessment to be in compliance with meaningful use. Their response was fast, the final report is detailed but simple and easy to follow. They were always available to answer our questions.
E. Compres
Pulmonary and Sleep Center of the Valley
I never miss the opportunity to learn something new …that’s why I am always registering to all free seminars offered on the web. databrackets (formerly EHR 2.0) happened to be the friendliest, comprehensive and up-to- date source of HIPAA Privacy and Security updates.
Alexandra V.
Community Healthcare Network
Today’s presentation was great! Thank you for sending the slides. My only feedback is that it would be fabulous to have the slides ahead of time so I could print them and take notes on the slides.Thanks for your time and knowledge today!
T.B., PM
Community Health Network
Particularly interesting was the flow chart on Administrative Simplification. I utilize all of the Security subcategories you list under the Security tile and appreciate knowing that I am hitting all of the relevant topics during my employee training.
Jessica B.
JD, CHC
I have re-worked our original risk assessment….We are using databrackets' (formerly EHR 2.0) Meaningful Use Security Risk Analysis Toolkit and it meets our needs. It was easy to use and I believe that it very beneficial to our meeting meaningful use.
Bill Curtis
Neurosurgical Associates Of Texarkana, TX
Information (webinars) presented by databrackets (formerly EHR 2.0) highlights some of today’s most demanding healthcare topics. The webinars help to direct those operating in today’s rapidly changing environment in the right direction.
Candace M.
Privacy and Security Officer, Springhill Medical Center
Our Growing List of Credentials
0
+
Assessments
0
+
Clients
0
+
Assessment Libraries
0
+
Years of Experience
0
+
No. of Staff Trained
0
+
HIPAA
0
+
SOC 2 Readiness
0
+
Pen Testing
0
+
ISO 27001 Certifications
0
+
Dollars Saved in Compliance Penalties