 A SOC 2 certification / examination is pursued by service organizations who want to prove to potential customers that they can manage their data effectively. Typically a SaaS provider, Managed Service Provider (MSP), Network service provider and other service providers select an authorized CPA firm and an authorized SOC 2 auditor in it, to audit their system. Usually, the process may be smooth if they go through a readiness prep assessment and then select a SOC 2 auditor who is familiar with their industry and customer requirements. However, sometimes, you may find yourself in a difficult situation during your SOC 2 audit and you may want to consider changing your SOC 2 auditor.
A SOC 2 certification / examination is pursued by service organizations who want to prove to potential customers that they can manage their data effectively. Typically a SaaS provider, Managed Service Provider (MSP), Network service provider and other service providers select an authorized CPA firm and an authorized SOC 2 auditor in it, to audit their system. Usually, the process may be smooth if they go through a readiness prep assessment and then select a SOC 2 auditor who is familiar with their industry and customer requirements. However, sometimes, you may find yourself in a difficult situation during your SOC 2 audit and you may want to consider changing your SOC 2 auditor.
A SOC 2 examination can be time consuming, and you can exceed your budget if it is not systematically planned. Sometimes, the challenges may arise from within the company and can lead to a blame game with the auditor. We highly recommend undergoing a SOC 2 readiness assessment, getting organized and vetting your SOC 2 auditor, to avoid such an occurrence.
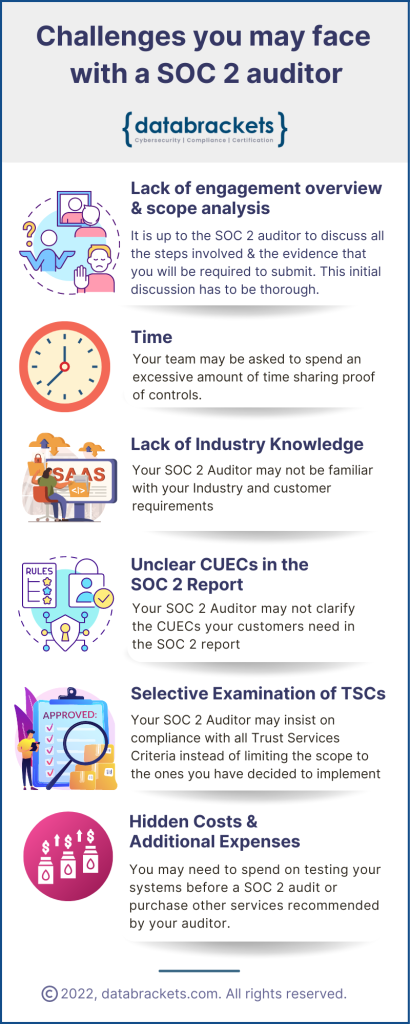
Challenges you may face with a SOC 2 auditor:
1) Lack of engagement overview & scope analysis
Your SOC 2 audit can be a relatively seamless experience when your evidence matches the SOC 2 controls and the Trust Services Criteria you want audited. After you agree on the scope of the audit and your customer requirements, it is up to the SOC 2 auditor to discuss all the steps involved and the evidence that you will be required to submit. If the scoping is not clearly defined at the start, the auditor can go out of scope. This can be particularly confusing for companies who are new to SOC 2 and who need a proper orientation to the process. The process has to be matured and you need to gauge the process maturity of the CPA firm before finalizing your contract to work with them.
SOC 2 audits need to be conducted annually. As a result some CPA Firms also mandate the continuity of work for 3-5 years in their contracts. The SOC 2 framework and AICPA does not mandate continuing with the same SOC 2 auditor after you complete your engagement. This is yet another area of conflict that needs to be discussed at the outset, so you are well-informed before you sign your contract to work with the authorized CPA Firm.
There can be several pitfalls and unnecessary obstacles in your SOC 2 journey if your initial discussions are not thorough and if your auditor does not guide you properly. This is the root cause for most of the challenges you may face. We recommend that you review the rest of the challenges and draft a set of questions to vet the SOC 2 auditor before you finalize who will conduct your SOC 2 audit.
2) Time
The time spent with a SOC 2 auditor can seem excessive and hamper your ability to manage daily business operations. This can be challenging since the auditor might request a lot of information for the SOC 2 report, which you may not know is required. For example: documented proof of the management’s engagement on security issues. Proving this can involve going through several meeting documents. Audit time is not defined for a SOC 2 examination as it is for an ISO certification and this might result in unpleasant surprises for your team.
Additionally, some auditors share a spreadsheet and ask you to email evidence documents. This system can be chaotic since you need to see the correlation between the controls and the evidence / documents.
One solution we recommend is engaging the services of a SOC 2 readiness assessment partner, like databrackets, to help you get organized before your engagement with an auditor. At the outset we invite you to share your evidence on our platform as per the controls and corresponding Trust Services Criteria you have selected. This helps you to work systematically and share the evidence further with your chosen auditor. A SOC 2 readiness assessment not only helps you to save time and effort but also ensures that you have someone to check your evidence / documents and share feedback before the actual SOC 2 audit.
3) Lack of Industry Knowledge
The purpose of a SOC 2 examination / SOC 2 certification is to prove to your customers that your systems will effectively manage their data. However, at times, your SOC 2 auditor may not be familiar with your industry, day-to-day operations, SLAs and customer expectations. As a result, they may not be able to produce the kind of report that meets your customer’s expectations. This defeats the purpose of getting certified and could lead to frustration since the actual consumer of the SOC 2 report is your customer / stakeholder. If they do not get the impression that you are the right vendor for them after reading the report, the whole exercise will seem counterproductive.
Lack of industry knowledge also impacts a critical part of the report – Complementary User Entity Controls (CUECs). We have discussed this at length in the next section.
4) Unclear Complementary User Entity Controls (CUECs) in the SOC 2 Report
A customized SOC 2 report clearly outlines the Complementary User Entity Controls or CUECs in the description of the customer’s system. These controls are intended for your customer – the actual consumer of the SOC 2 report. They inform your customer about the controls they need to implement in their systems to properly use your services.
A SOC 2 auditor who is familiar with your industry can explain these CUECs in the SOC 2 Report. This is critical since the level of security, availability, privacy, confidentiality and processing integrity of your system can only be maintained when it is properly configured in the systems used by your customer. If your SOC 2 auditor does not understand your service requirements and which CUECs are critical in your industry, you may receive a SOC 2 report that does satisfy your customers and meet your objectives.
5) Selective examination of Trust Services Criteria
The SOC 2 framework permits clients to focus on the Trust Services Criteria which they want audited and exclude the rest. This flexibility exists since the SOC 2 Report outlines at the start which criteria and controls are being examined and then showcases if they function at optimal levels or not. SOC 2 allows you to select the Trust Services Criteria which you want to showcase. By using this method, the client’s customers are informed and empowered to take a decision to work with the client or not. While this is the ideal situation, if your SOC 2 auditor is unwilling to accept your decision, even when the rules permit, you may face a difficult situation. Your SOC 2 auditor may insist on an audit of all the Trust Services Criteria and not respect the flexibility accorded by the SOC 2 framework,
6) Hidden Costs and Additional Expenses
SOC 2 audits are done by authorized CPA firms who may have sister concerns or partners who offer other services which may be helpful to your company. Sometimes, your SOC 2 auditor may try to up-sell / cross sell these services aggressively, under the guise of good advice. This can lead to a conflict and unplanned expenses.
Before your SOC 2 audit, you may also be advised to undergo penetration testing to check the security of your systems. This can be yet another hidden cost, which you can predict with a SOC 2 readiness assessment.
Each of these challenges are severe and it is important to avoid the possibility of going through any of them. Through this blog, we hope that you have been empowered to foresee potential pitfalls and vet the SOC 2 auditor in the introductory meeting, ask for a sample report for your industry, review the terms of the contract you will sign and follow-up on their references before you begin your engagement.
How databrackets can support your SOC 2 Journey
Experts at databrackets have extensive experience in supporting organizations align their processes with AICPA’s Trust Services Criteria and prepare for a SOC 2 Audit. If you would like to connect with an expert to better understand SOC 2 and plan your SOC 2 journey, do not hesitate to schedule a consultation.
Related Links:
Srini Kolathur
Srini is the Director of databrackets.com. He is a results-driven security and compliance professional with over 25 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are CMMC, SOC 2, ISO 27001, FedRAMP, NIST SP 800-171, NIST SP 800-53, NIST Cybersecurity Framework (CSF), HIPAA, Security Risk Assessments, among others. He is a Lead CCA for CMMC, CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE. He has verified all the technical information in this blog and co-authored it with Aditi Salhotra.