Pen testing for CMMC answers the question your SPRS score never had to answer before. Do your security controls actually work under real attack conditions, or do they just look good on paper?
This blog focuses on pen testing for CMMC where it has real consequences: Level 2 Certification by a C3PAO and Level 3 Certification by the DIBCAC, the only scenarios where an external party formally evaluates your security controls. We focus on what your C3PAO needs from your pen testing program, and what Level 3 Certification by the DIBCAC demands. We have also included guidance for Level 1 and Level 2 contractors who are required to self-attest.
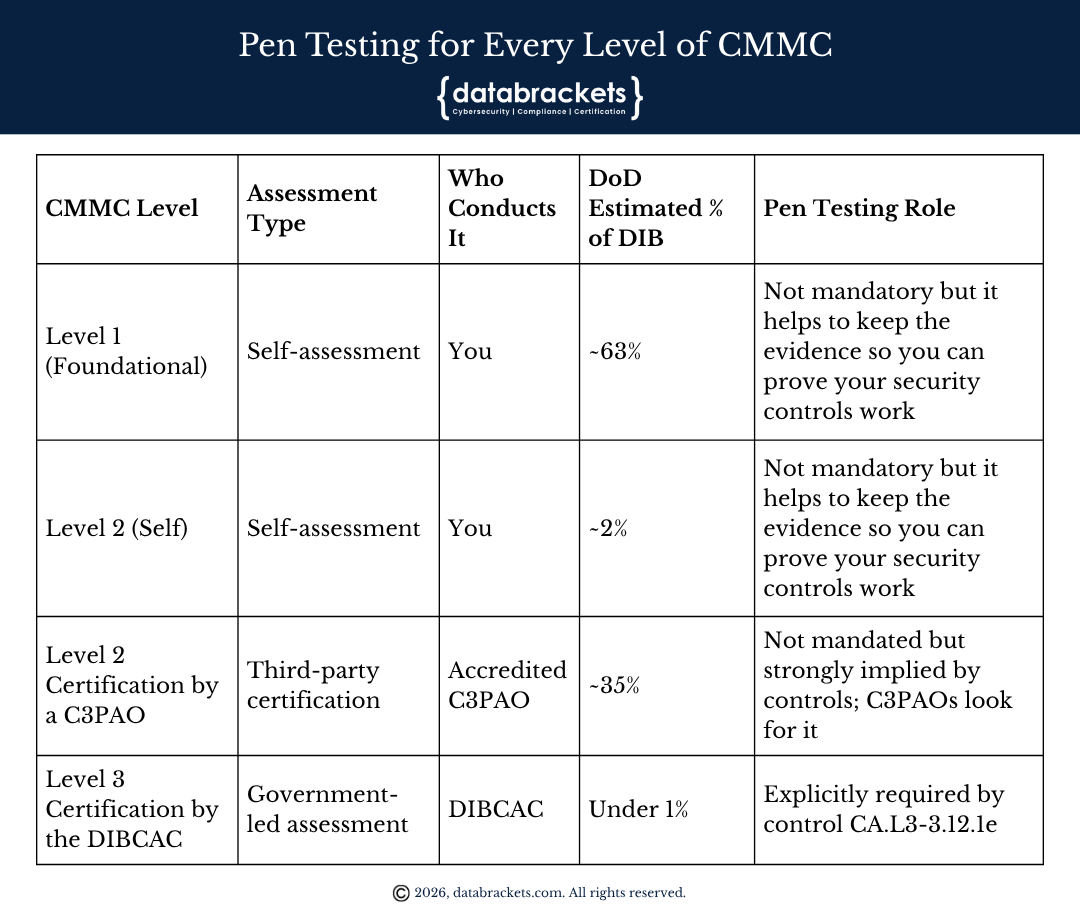
Pen Testing for every Level of CMMC
CMMC applies to every defense contractor handling FCI or CUI. What differs for each of the three CMMC levels is the number of security controls required and whether you need a self-assessment or a formal certification. The DoD has published its own estimates for how many contractors fall into each bucket, and those numbers matter for understanding the urgency you face.
This blog focuses on pen testing for CMMC where it has real consequences: Level 2 Certification by a C3PAO and Level 3 Certification by the DIBCAC, the only scenarios where an external party formally evaluates your security controls. We focus on what your C3PAO needs from your pen testing program, and what Level 3 Certification by the DIBCAC demands. We have also included guidance for Level 1 and Level 2 contractors who are required to self-attest.
The DoD estimates approximately 35% of the defense industrial base, roughly 76,598 contractors, will need Level 2 Certification by a C3PAO. These are the organizations handling Controlled Unclassified Information under defense-category contracts. Another 63% handle only Federal Contract Information and self-assess at Level 1. A small 2% handle non-defense-category CUI and self-assess at Level 2. Fewer than 1% of the entire DIB will require Level 3 Certification by the DIBCAC. Importantly, Level 3 Certification by the DIBCAC is not a standalone path. It requires Final Level 2 Certification by a C3PAO first, meaning all 110 NIST SP 800-171 controls must be fully MET before a Level 3 assessment can begin. Level 3 then adds 24 controls from NIST SP 800-172 on top of that foundation.
Stated plainly, if you handle defense CUI, you are most likely in that 35%. A C3PAO is coming to verify your controls. No one is taking your SPRS score at face value anymore.
Scope and Types of Pen Testing for CMMC Level 2 and Level 3
Before discussing what your C3PAO or DIBCAC assessment requires in detail, every contractor needs to understand two things: what systems fall inside your pen test scope, and what type of testing is appropriate for your level. Getting either wrong produces evidence that does not hold up during formal certification.
For Level 2 Certification by a C3PAO, the scope of pen testing for CMMC must align directly with your CMMC assessment boundary. That boundary includes CUI Assets, which are any systems that process, store, or transmit Controlled Unclassified Information. It also includes Security Protection Assets, meaning the systems that protect your CUI environment such as firewalls, identity and access management infrastructure, log management tools, and authentication servers. Specialized Assets within that boundary, including operational technology and IoT devices that interact with your CUI environment, must also fall within scope. Testing only your external perimeter while leaving internal CUI-handling systems untouched is one of the most common scoping failures C3PAOs encounter.
On the types of pen testing relevant to Level 2 Certification by a C3PAO, network penetration testing covers your internal and external network infrastructure and is the foundation of any compliant engagement. Web application penetration testing is required when your organization uses custom-developed software to process, store, or transmit CUI, because Requirement 3.11.2 specifically addresses the need for dynamic analysis of such applications beyond automated scanning. Internal penetration testing, which simulates an attacker who has already gained access inside your perimeter, is critical for demonstrating that lateral movement toward CUI is restricted and that access controls function as documented in your SSP. Each of these test types produces distinct evidence that maps to different NIST SP 800-171 controls, and your C3PAO will evaluate that evidence against the specific controls it is intended to satisfy.
For Level 3 Certification by the DIBCAC, the scope requirements are the same as Level 2 but the stakes are higher because all 110 Level 2 controls must already be MET before the Level 3 assessment begins. Every asset in scope for your Level 2 Certification by a C3PAO remains in scope for your Level 3 Certification by the DIBCAC. What changes is the depth and methodology of the testing itself.
On the types of pen testing required for Level 3 Certification by the DIBCAC, standard network and application testing is a baseline, not a ceiling. Control CA.L3-3.12.1e sits within NIST SP 800-172’s penetration-resistant architecture strategy, which means testing must go further. Red team exercises, which simulate a full adversary campaign from initial access through lateral movement and data exfiltration, are the appropriate methodology at this level. Adversary simulation based on MITRE ATT&CK techniques used by nation-state actors targeting the defense industrial base is not optional at Level 3, it is the intent of the control. Assumed breach scenarios, where testers begin with a foothold already established inside your environment, test whether your detection and response capabilities function under real attack conditions. Purple team engagements, where testers and your defensive team work together to measure and improve detection coverage, are also appropriate at Level 3 because CA.L3-3.12.1e is designed to validate that your entire security architecture holds against advanced persistent threats, not just that your perimeter is intact.
Level 2 Certification by a C3PAO
Here is the real situation for most contractors in the defense industrial base. You have been submitting an SPRS score under DFARS 252.204-7012 since it became required. That score is self-reported. Nobody came to check it. CMMC changes that entirely. A C3PAO, an accredited Certified Third-Party Assessment Organization, will now independently verify whether your 110 NIST SP 800-171 controls are actually implemented and actually working.
The gap between what contractors self-report and what C3PAOs find during formal assessment is the central problem that CMMC was designed to close. Pen testing for CMMC at Level 2 is one of the most powerful tools you have for closing that gap before the C3PAO arrives.
One point confuses many contractors: neither your C3PAO nor your RPO conducts the pen test. The C3PAO’s job is to independently evaluate your compliance, not to test your security. An RPO, or Registered Practitioner Organization, helps you prepare for certification. Performing penetration testing is not part of what an RPO delivers. Engaging a separate, qualified penetration testing firm is entirely your responsibility. That firm tests your environment, produces the findings, and hands the evidence to you. Bring that evidence to your C3PAO assessment.
Level 2 does not contain a sentence that says “you must conduct a penetration test.” However, three NIST SP 800-171 requirements collectively make pen testing the most practical way to build the evidence your C3PAO will look for.
Requirement 3.11.2 requires periodic vulnerability scanning of information systems and applications, with action taken when new vulnerabilities are identified. For custom software processing CUI, this extends to dynamic testing beyond automated scanning. Pen testing for CMMC satisfies this requirement far more thoroughly than any scanner can.
Requirement 3.12.1 is where the real weight sits. It requires periodic assessment of security controls to determine whether they are working as intended. C3PAOs evaluate evidence using three methods: Examine (reviewing documents), Interview (questioning your team), and Test (directly evaluating controls). A penetration test produces Test-method evidence for multiple controls at once. Show up without pen test evidence and you hand your C3PAO a gap in the strongest evidence category they use.
Requirement 3.12.3 requires ongoing monitoring of security controls. Quarterly scanning handles part of this. Pen testing for CMMC on a regular schedule, with documented remediation and verification retesting, builds the continuous monitoring evidence trail that satisfies both 3.12.1 and 3.12.3 together.
C3PAOs routinely request recent pen test reports during the evidence review phase. Your C3PAO is not required to fail you for lacking one at Level 2. But the absence creates a visible hole in your Test-method evidence at precisely the controls that carry the most scrutiny. That is a risk you can avoid.
Level 3 Certification by the DIBCAC
Level 3 Certification by the DIBCAC is reserved for contractors supporting the most critical national security programs, those that the DoD has determined are actively targeted by Advanced Persistent Threats, sophisticated and often state-sponsored adversaries. Fewer than 1% of the defense industrial base reaches this tier. If you are in it, you already know it, and pen testing for CMMC at this level is not a judgment call.
Before DIBCAC conducts your Level 3 Certification assessment, you must first hold the Final Level 2 Certification by a C3PAO for the same information systems. There is no path from Level 2 (Self) to Level 3 Certification by the DIBCAC. The prerequisite is specific, formal, and non-negotiable. Final Level 2 Certification by a C3PAO requires all 110 NIST SP 800-171 controls to be fully MET and verified. Level 3 then adds 24 controls from NIST SP 800-172 on top of that complete foundation. This is not a parallel path. Level 3 contractors are responsible for every Level 2 requirement and every Level 3 requirement, and both must be in place before certification is complete.
Once that prerequisite is met, the governing pen testing requirement is control CA.L3-3.12.1e. This control sits in the Security Assessment domain and draws from NIST SP 800-172 Requirement 3.12.1e. NIST SP 800-172 is the enhanced security publication that supplements the 110 NIST SP 800-171 controls with 24 additional requirements designed specifically to counter APT-level attacks. CA.L3-3.12.1e requires organizations to employ penetration testing to validate the effectiveness of security controls. Testing must occur at least once a year, or whenever significant security changes are made to relevant systems.
A NOT MET finding on CA.L3-3.12.1e during your Level 3 Certification assessment produces Conditional Level 3 status, not Final. Conditional status allows a POA&M, which is a Plan of Action and Milestones, a formal remediation tracking document, for up to four of the 24 Level 3 controls. All Level 3 POA&M items must be resolved and verified by DIBCAC within 180 days of your Conditional status date. Miss that deadline and your Conditional status expires entirely, along with your eligibility for the contracts tied to it.
CA.L3-3.12.1e is not on the list of POA&M-prohibited controls under 32 CFR 170.21, so it can technically appear on a POA&M. But carrying annual pen testing as an open remediation item means you have never actually run a compliant test, and the 180-day closeout window is firm. The practical answer is simple: have your pen testing program running before your Level 3 Certification assessment begins.
Furthermore, Level 3 pen testing for CMMC is not a standard commercial engagement. NIST SP 800-172 places CA.L3-3.12.1e within a penetration-resistant architecture strategy. Testers must simulate the specific tactics, techniques, and procedures used by APT actors. Generic scanning tools and standard vulnerability assessments do not satisfy this. As a result, Level 3 pen testing for CMMC requires testers with real APT expertise and threat-informed methodology, including working knowledge of MITRE ATT&CK behaviors relevant to defense contractor environments.
The Level 3 Certification assessment requires a complete evidence chain: the test report, remediation records, and documentation demonstrating that testing recurs on schedule. Missing any element of that chain produces a NOT MET finding for CA.L3-3.12.1e.
Pen Testing vs. Vulnerability Scanning
This confusion shows up constantly in CMMC preparation, and it causes real compliance gaps. Many contractors believe they have satisfied their security assessment obligations because they run quarterly scans. They have not.
Vulnerability scanning checks your environment against a database of known weaknesses. A scanner reads your systems and flags what it recognizes. It produces a list. Your team reviews the list, patches what it can, and closes tickets. This is necessary work, and it satisfies Requirement 3.11.2. But a scanner cannot tell you whether an attacker could actually get in, escalate privileges, move laterally, and reach your CUI. It only reports what it was programmed to look for.
Penetration testing puts a skilled professional in the role of the attacker. Testers chain vulnerabilities together the way a real adversary would. An individual misconfiguration that looks minor in isolation can become a critical access path when combined with two other weaknesses a scanner catalogued separately. Logic flaws in custom applications, excessive trust between systems, and lateral movement opportunities all surface during pen testing and almost never show up in scan reports.
For CMMC purposes, the distinction matters in direct, practical ways. At Level 3 Certification by the DIBCAC, scan results do not satisfy CA.L3-3.12.1e. Period. At Level 2, presenting scan results alone when a C3PAO asks for security assessment evidence is the difference between a strong MET finding and a weak one. C3PAOs know the difference between Test-method evidence and a scan report, and they score them accordingly. Run both. Neither substitutes for the other.
Factor | Penetration Testing | Vulnerability Scanning |
Method | Human-led exploitation of identified weaknesses | Automated detection of known weaknesses |
Output | Exploited findings with proof-of-impact evidence | Ranked list of potential vulnerabilities by severity |
CMMC relevance | Required by CA.L3-3.12.1e at Level 3 Certification by the DIBCAC; best evidence for 3.12.1 at Level 2 | Supports 3.11.2 at Level 2; insufficient alone at Level 3 Certification by the DIBCAC |
Frequency | Annual minimum at Level 3 Certification by the DIBCAC; risk-based at Level 2 | At minimum quarterly for Level 2 |
Who performs it | Qualified external security professionals | Can be run internally with appropriate tools |
Evidence value in assessment | High; produces Test-method evidence for multiple controls | Moderate; confirms detection capability only |
What Your Pen Test Evidence Needs to Look Like
Your pen test produces a report. That report is not the end product for CMMC purposes. The full evidence chain your C3PAO needs, or that Level 3 Certification by the DIBCAC requires, runs deeper than the report itself.
Start with scope documentation. The test scope must align with your CMMC assessment scope: CUI Assets, Security Protection Assets, and Specialized Assets. A pen test that covered only your external perimeter while your internal CUI-handling systems went untested is a scoped gap that will surface during your assessment.
The report itself must document each finding clearly: what was exploited, what access was gained, and what the potential impact on CUI would have been. Severity ratings alone are insufficient. The evidence must show that your team understood what was found and what it meant.
Next, you need remediation records. Each finding requires a documented fix with a completion date. This is where many organizations fall short. They get the report, patch the issues, and move on without formal documentation. Consequently, by the time their C3PAO arrives, they cannot demonstrate that the pen test led to any particular remediation action.
Verification retesting closes the evidence chain. A follow-up test, or at minimum a targeted retest of the specific findings, confirms the vulnerabilities were actually resolved. This is the verification evidence that transforms a pen test from a point-in-time activity into an ongoing security practice.
Every piece of this chain must connect to your System Security Plan. The SSP documents how your organization implements required controls. When pen testing reveals a gap, that gap must appear in the SSP as updated implementation language or in your POA&M as a tracked remediation item. C3PAOs will cross-reference these documents. An inconsistency between your pen test findings and your SSP raises questions about the accuracy of everything else in the plan.
Building Your Program Before the Window Closes
About 76,598 contractors need Level 2 Certification by a C3PAO. As of early 2026, approximately 1,042 have completed the process, according to the Cyber AB Town Hall data from February 2026. There are roughly 80 authorized C3PAOs to serve that demand, and booking windows are stretching to three to six months already in many cases. The contractors who wait until a solicitation requires CMMC certification before they start preparing are effectively choosing to miss the contract.
Start your pen testing program at least 12 months before your anticipated certification date. Remediation after findings takes time. Verification retesting takes additional time. Documentation of the full cycle must be complete before assessment day. Twelve months sounds like a long runway until you account for finding an available C3PAO, scheduling the pen test, managing the remediation of multiple findings, and producing documentation that holds up to formal review.
Selecting testers who understand the CMMC framework specifically is not optional; it is the difference between a report you can use as evidence and a report you cannot. Generic reports produced against standard penetration testing frameworks without explicit mapping to NIST SP 800-171 or 800-172 controls are harder for C3PAOs to evaluate. Ask testers directly how they will map findings to control requirements in the deliverable before you engage them.
At Level 3 Certification by the DIBCAC, testers must understand APT actor behavior. Standard commercial pen testing methodology is insufficient for CA.L3-3.12.1e. Require demonstrated knowledge of MITRE ATT&CK behaviors relevant to defense contractor environments, including techniques used by nation-state actors targeting the defense industrial base.
Connect your pen test to your existing compliance documentation. Findings go into the SSP or POA&M. Remediation gets tracked and closed formally. Retesting produces verification records. This documentation cycle is what your C3PAO reads, and it is how a mature, functional security program looks compared to one that ran a test, filed the report, and hoped for the best.
Guidance for Level 1 and Level 2 Contractors (Self-Attestation)
If you self-assess at Level 1 or Level 2 (Self), no external party will come to check your pen test documentation. There is no legal pen testing requirement at either path. This section is shorter because the stakes are different.
However, two practical realities are worth considering. First, your SPRS score is visible to prime contractors, and primes are increasingly asking subcontractors for evidence beyond a posted score. Pen testing for CMMC at self-assessment levels gives you something concrete to point to when a prime asks how you verified your controls actually work.
Second, contracts grow. A Level 1 organization today can win a CUI contract tomorrow and suddenly face Level 2 Certification by a C3PAO. Starting a basic pen testing practice now, before the pressure arrives, means your remediation is already behind you before a C3PAO ever arrives. Discovering significant vulnerabilities three months before your certification assessment is a painful and avoidable situation. Discovering them two years ahead of time is simply good security.
Summary
Pen testing for CMMC is not a universal requirement, but it is a critical one for most contractors who touch defense contracts. The DoD estimates roughly 35% of the defense industrial base, approximately 76,598 contractors, face Level 2 Certification by a C3PAO, and fewer than 1% face Level 3 Certification by the DIBCAC. Those are the two scenarios where an external party evaluates your security controls, and those are the two scenarios where your pen testing program determines whether you pass.
At Level 2 Certification by a C3PAO, pen testing is not explicitly mandated but it is the most direct way to produce the Test-method evidence that C3PAOs look for under Requirements 3.11.2, 3.12.1, and 3.12.3. Show up without pen test evidence and your C3PAO is scoring your most scrutinized controls from the weakest possible evidence category.
At Level 3 Certification by the DIBCAC, control CA.L3-3.12.1e from NIST SP 800-172 Requirement 3.12.1e requires annual penetration testing. The testing must be threat-informed and conducted by professionals who understand APT actor behavior. A NOT MET finding produces a Conditional status and a 180-day remediation window. Letting that window close without resolving it ends your Level 3 Certification by the DIBCAC. An OSC cannot reach Level 3 Certification by the DIBCAC without first holding Final Level 2 Certification by a C3PAO for the same systems, meaning all 110 NIST SP 800-171 controls must be fully MET before a Level 3 assessment can even begin.
The gap between pen testing and vulnerability scanning is not a matter of preference. Scanning finds known weaknesses in current configurations. Pen testing proves whether your controls actually hold when someone tries to break them. C3PAOs evaluate these differently, and they score them differently.
Phase 2 begins November 10, 2026, making Level 2 Certification by a C3PAO mandatory for applicable contracts. Full enforcement across all applicable contracts follows by November 10, 2028. The contractors who have pen testing programs running, evidence chains documented, and SSPs that match reality will move through their certifications. Those who are still running quarterly scans and calling it done will not.
Key Takeaways
- Know your assessment type before you build anything. Your contract solicitation specifies whether you face Level 2 (Self), Level 2 Certification by a C3PAO, or Level 3 Certification by the DIBCAC. Only the last two involve an external party. Only those two make pen testing evidence something that someone other than you will evaluate. Build your testing program to the standard your actual path requires.
- If you face Level 2 Certification by a C3PAO, treat Requirements 3.12.1, 3.11.2, and 3.12.3 as your pen testing roadmap. These three requirements are where C3PAOs focus their Test-method evidence review. A pen test and its documented remediation cycle address all three simultaneously. No other single activity does that.
- For Level 2 Certification by a C3PAO, your pen test scope must cover CUI Assets, Security Protection Assets, and Specialized Assets. Testing only your external perimeter is a scoping failure that C3PAOs will identify. Network penetration testing, internal penetration testing, and web application testing for any custom software processing CUI are the three types of testing relevant at this level. Each maps to specific NIST SP 800-171 controls that your C3PAO will evaluate.
- If you face Level 3 Certification by the DIBCAC, CA.L3-3.12.1e is a legal requirement with a hard calendar attached. Annual pen testing must be operational before your Level 3 Certification assessment begins. A NOT MET finding puts you on a 180-day conditional clock. You also need Final Level 2 Certification by a C3PAO before DIBCAC will conduct your Level 3 Certification. That means all 110 NIST SP 800-171 controls must be fully MET and verified before you can even request a Level 3 assessment. Level 3 adds 24 controls on top of that complete foundation. Plan your timeline accordingly.
- For Level 3 Certification by the DIBCAC, standard network testing is a baseline, not a ceiling. Red team exercises, adversary simulation using MITRE ATT&CK techniques relevant to nation-state actors, assumed breach scenarios, and purple team engagements are the appropriate methodology. CA.L3-3.12.1e requires you to validate your entire security architecture against advanced persistent threats, not just confirm your perimeter is intact.
- Start 12 months before your anticipated certification date. Remediation, verification retesting, and documentation all take time you do not have if you start three months out. With approximately 76,598 contractors chasing roughly 80 authorized C3PAOs, scheduling delays alone will consume months you cannot spare.
- Build the full evidence chain, not just the test report. Scope documentation, the report itself, remediation records with completion dates, verification retesting results, and SSP updates that reflect what was found. Your C3PAO reads all of it. The absence of any piece weakens the entire package.
- Select testers who can map findings to NIST SP 800-171 or 800-172 control requirements. A generic pen test report written for a corporate security audience is not the same as one written to serve as CMMC compliance evidence. Require control mapping in the deliverable before you sign the engagement.
- Run vulnerability scanning and pen testing for CMMC as separate programs. Scanning satisfies the frequency requirements of 3.11.2 and should run at least quarterly. Pen testing validates whether your controls hold under actual attack conditions and satisfies 3.12.1. One does not replace the other. Running only one of these leaves a gap that your C3PAO will find.
- Level 1 and Level 2 (Self) contractors have no external party reviewing their work today, but prime contractors are watching. Primes are asking subcontractors for evidence beyond an SPRS score. Contracts grow, and the Level 2 Certification by a C3PAO you avoid today may become unavoidable tomorrow. Pen testing for CMMC now means your remediation is behind you when the stakes go up.
How databrackets can help you with Pen Testing for CMMC
databrackets is an authorized C3PAO and independent consulting organization for CMMC. We offer Certification OR Readiness and Consulting services for CMMC. To avoid a conflict of interest and abide by CMMC’s independence requirements, we do not offer both services to the same client. We offer Pen Testing services for CMMC as part of our Consulting services and not as a C3PAO.
We are an ideal partner for either service since we bring over 15 years of proven expertise in helping organizations achieve compliance or certification with the most rigorous cybersecurity and data privacy standards, including ISO 27001, SOC 2, HIPAA, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, and CMMC. We are an authorized certifying body for ISO 27001 and 3PAO for FedRAMP.
Schedule a Consultation to work with us as your C3PAO for CMMC Certification or as your Compliance Partner to help you prepare for it.
A. Why Choose databrackets as your C3PAO
1. Proven Multi-Framework Expertise
What makes databrackets particularly valuable is our extensive experience across complementary frameworks, including NIST SP 800-171, NIST SP 800-53, SOC 2, ISO 27001, HIPAA, and NIST Cybersecurity Framework. We are also an authorized certifying body for ISO 27001 and 3PAO for FedRAMP.
This breadth of knowledge enables our assessment teams to understand how CMMC controls integrate with your existing compliance efforts and identify synergies that strengthen your overall security posture.
2. Technical Environment Proficiency
databrackets’ assessment team of CCAs and CCPs has the specialized technical competence essential for accurate CMMC evaluations. Our experience spans diverse technological environments, from traditional on-premises infrastructures to complex cloud deployments, ensuring we can effectively assess whatever technical landscape your organization operates in.
3. Strategic Timeline Management
With proven capability in managing sophisticated assessments spanning the typical 4–8-week timeframe, databrackets understands how to minimize disruption to your operations while ensuring comprehensive evaluation of all 110 NIST SP 800-171 security controls.
As a authorized C3PAO with extensive cybersecurity and compliance experience, databrackets offers a deep understanding of the CMMC assessment process. This comprehensive expertise enables us to conduct thorough assessments with clear explanations of findings and methodologies, resulting in more insightful evaluations for organizations seeking certification.
To inquire about our C3PAO Services, contact our team at sales@databrackets.com or schedule a free consultation.
B. Why Choose databrackets for Your CMMC Compliance Journey
We specialize in transforming CMMC compliance from a daunting obstacle into a strategic business enabler.
Proven Track Record: Over 14 years supporting organizations across diverse industries with complex compliance requirements
Comprehensive Approach: End-to-end support from initial assessment through ongoing compliance
Industry Recognition: Authorized certifying body for ISO 27001 and 3PAO for FedRAMP
Strategic Partnership: We don’t just help you achieve compliance—we help you leverage it for competitive advantage.
Our Comprehensive CMMC Compliance Services include:
1. Strategic Planning & Assessment:
CMMC readiness assessments and comprehensive gap analysis
CUI system boundary definition and scoping guidance
Network architecture documentation and CUI flow diagrams
Risk assessment and vendor compliance evaluations
2. Implementation & Documentation Support:
System Security Plan (SSP) development and customization
Complete policy and procedure documentation suite
FIPS validation documentation and shared control matrices
Evidence collection strategies and management systems
3. Assessment Preparation:
Mock assessments and readiness validation
CMMC documentation optimization and organization
Personnel training and assessment preparation
C3PAO coordination and selection support
4. Ongoing Compliance:
Continuous monitoring and compliance maintenance
Annual affirmation support and triennial assessment preparation
Change management and configuration control guidance
Customized CUI awareness training programs
For immediate assistance with your CMMC compliance journey, contact our certified experts at sales@databrackets.com or schedule a free consultation.
Helpful Resources:
https://databrackets.com/blog/how-to-select-the-right-c3pao-for-your-cmmc-certification/
Srini Kolathur
Co-Author: Aditi Salhotra
Manager – Digital Marketing and Business Development
Aditi is a Digital Marketing and Business Development Professional at databrackets.com. She is a strong advocate of good cyber hygiene and is proud of the company’s mission to safeguard organizations from cyber threats and ensure their business continuity in adverse situations.