The in-depth answer: The Health Insurance Portability and Accountability Act (HIPAA) sets the minimum standards for protecting sensitive patient health information (PHI). The Department of Health and Human Services (HHS) regulates HIPAA compliance, while the Office for Civil Rights (OCR) enforces it. The OCR regularly publishes recommendations on new issues affecting healthcare and investigates common HIPAA violations on a regular basis. However, a HIPAA-compliant organization can still be a target for a ransomware attack. Despite having advanced cybersecurity measures in place to comply with HIPAA, no organization is fully impervious to all cyber threats.
Ransomware Attacks in a HIPAA-compliant Organization
HIPAA regulations mandate that healthcare providers protect the privacy and security of patient’s health information. This involves implementing safeguards such as access controls, audit controls, integrity controls, and transmission security. However, these measures primarily focus on ensuring data privacy and security, and although they can help reduce the risk of ransomware attacks, they do not eliminate it completely.
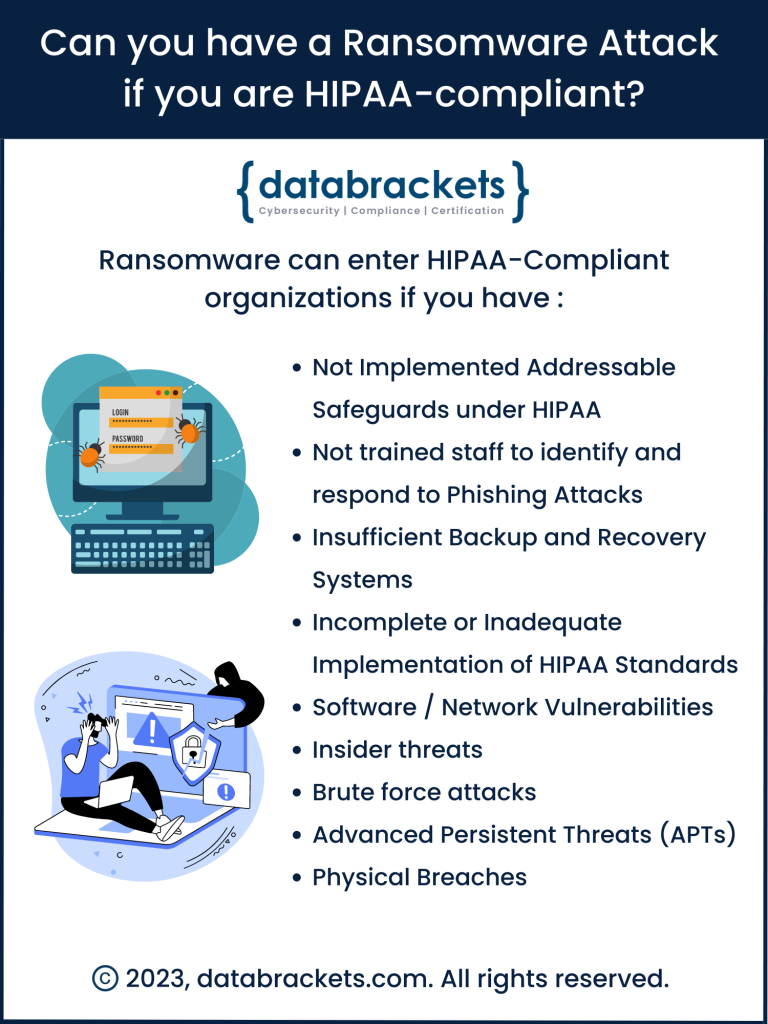
Ransomware is malicious software that encrypts the victim’s data. Hackers demands a ransom to restore access to the data once they are paid. They also have the ability to modify the data and sell it, even if they are paid the ransom amount. This leads to serious complications in the Healthcare Industry since their data is targeted due to its critical importance for its high value. Even with HIPAA-compliant measures in place, organizations can fall victim to ransomware attacks via various methods:
-
Not implementing addressable safeguards:
Organizations tend to overlook implementing addressable safeguards outlined in the HIPAA Security Rule. These safeguards focus on Authorization / Supervision, Workforce Clearance Procedures, Termination Procedures, Access Authorization, Security Reminders, Log-in Monitoring, Password Management, Protection from Malicious Software, Testing Contingency Plans, etc. Due to this oversight, their systems have vulnerabilities that can be exploited through a targeted cyber attack.
-
Phishing attacks:
One of the most common ways attackers can breach security defenses is through phishing emails. These emails trick employees into clicking on malicious links or attachments that install ransomware on the network.
-
Insufficient Backup and Recovery Systems:
HIPAA requires that covered entities have backup and disaster recovery measures in place. However, if these measures are not adequately and continuously maintained, tested, and updated, ransomware can infect not only the primary data systems but also backup systems, making data recovery impossible without paying the ransom.
-
Incomplete or Inadequate Implementation of HIPAA Standards:
Compliance doesn’t always mean complete protection. Organizations may meet the letter of the law without effectively securing all possible points of vulnerability. For instance, they might overlook the security of medical devices, partner networks, or other systems that connect to their main network.
-
Exploiting software vulnerabilities:
Cybercriminals often exploit known vulnerabilities in software applications that are not patched or updated regularly. Through these vulnerabilities, they gain unauthorized access and deploy ransomware.
-
Insider threats:
Employees, vendors, or other insiders with malicious intent or those who are simply careless may inadvertently expose the organization to ransomware attacks deliberately.
-
Brute force attacks:
In this method, attackers try numerous combinations to guess passwords and gain access to systems or networks. Once they are in, they install ransomware and infiltrate the entire network.
-
Advanced Persistent Threats (APTs):
These are long-term targeted attacks where cybercriminals infiltrate networks to mine data or disrupt services. They can plant ransomware and activate it at the most opportune moment. For example, zero-day exploits take advantage of security vulnerabilities that are unknown to the organization and the public. Such vulnerabilities are thus unpatched, making them a lucrative target for attackers.
-
Network vulnerabilities:
Weaknesses in network security, such as unsecured Wi-Fi networks or inadequate firewall protection, can create entry points for ransomware.
-
Physical breaches:
Access to physical machines (like a stolen laptop that has not been encrypted) can also lead to a breach. HIPAA requires physical safeguards, but like all security measures, they’re not 100% foolproof.
This list is not exhaustive, and HIPAA compliance can help mitigate these risks through required security measures like regular risk assessments, encryption of electronic protected health information (ePHI), maintaining updated and patched systems, and conducting regular staff training on cybersecurity best practices.
However, the cyber security challenges that organizations face are dynamic. They need a comprehensive approach to cybersecurity that goes beyond just HIPAA compliance. This might involve extensive and customized employee training to recognize phishing attempts, regular audits, and penetration tests to identify and patch vulnerabilities, the use of advanced threat detection and response systems, and robust, isolated backup systems to ensure data can be restored in the event of a ransomware attack. In addition, establishing an incident response plan can help minimize damage if an attack occurs.
Despite all these measures, it’s important to remember that no organization can be completely immune to ransomware attacks. Therefore, continuous improvement of your security posture and preparedness for potential attacks is critical.
In the event of a ransomware attack, HIPAA mandates specific steps and reporting procedures, including notifying affected individuals, the Department of Health and Human Services, and potentially the media depending on the scale of the breach. Therefore, compliance does not guarantee the prevention of attacks, but it does establish a strong foundation for preventing, detecting, and responding to such cyber threats, thereby reducing the possibility of risks in the long run.
How databrackets can help you create a secure IT infrastructure
Experts at databrackets have extensive experience working with Healthcare Providers, Cyber Liability Insurance Providers, Managed Service Providers (MSPs), FDA Regulated industries etc. Our services range from Security Risk Analysis, HIPAA compliance, Pen Testing & Vulnerability Scans, Implementation of Cyber Security Technology, Managed Security Services, and Security Risk Analysis for MIPS, among others.
Our team has supported organizations across a wide variety of industries to align their processes with security frameworks like HIPAA, 21 CFR Part 11, ISO 27001, SOC 2, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC etc.
We are constantly expanding our library of assessments and services to serve organizations across industries. Schedule a Consultation if you would like to Connect with an Expert to understand how we can customize our services to meet your specific requirements.
Related Links
Sources of Ransomware Attacks on Healthcare Systems
Protect your DICOM from Cyber Attacks
Security Tech Investments for Top 10 trends in 2023
How to Select a Security Vendor
Author: Aditi Salhotra, Digital Marketing and Business Development, databrackets.com
Aditi is a Digital Marketing and Business Development Professional at databrackets.com. She graduated with honors in Marketing from Sheridan College, Canada. In addition to her current profile, she contributes to Product Development and Content Creation. She is a strong advocate of Good Cyber Hygiene and white hat SEO techniques. She is proud of the company’s mission to safeguard organizations from cyber threats and ensure their business continuity in adverse situations.
Technical Expert: Srini Kolathur, Director, databrackets.com
The technical information presented in this blog has been carefully reviewed and verified by our Director, Srini Kolathur. Srini is results-driven security and compliance professional with over 20 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are SOC 2, ISO 27001, NIST 800-171, NIST 800-53, NIST Cybersecurity Framework, HIPAA, Security Risk Assessment, CMMC 2.0 among others. He is a CMMC Registered Practitioner (RP), CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE.
Experts at databrackets have extensive experience working with Healthcare Providers, Cyber Liability Insurance Providers, Managed Service Providers (MSPs), FDA Regulated industries etc. Our services range from Security Risk Analysis, HIPAA compliance, Pen Testing & Vulnerability Scans, Implementation of Cyber Security Technology, Managed Security Services, and Security Risk Analysis for MIPS, among others.
Our team has supported organizations across a wide variety of industries to align their processes with security frameworks like HIPAA, 21 CFR Part 11, ISO 27001, SOC 2, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC etc.
We are constantly expanding our library of assessments and services to serve organizations across industries. Schedule a Consultation if you would like to Connect with an Expert to understand how we can customize our services to meet your specific requirements.