 How do you prevent cyberattacks from impacting your business operations? This is the big question organizations have been asking in the wake of growing cyberattacks across industries. A growing number of data breaches have led to loss of customer data, disruptions in services, significant financial losses in addition to penalties and fines by regulatory bodies, loss of brand reputation, along with a host of other damaging outcomes. As cybersecurity and compliance experts, we decided to take a preventative approach and help businesses learn about the ways they can avoid a cyberattack from paralyzing their operations and damaging their revenue.
How do you prevent cyberattacks from impacting your business operations? This is the big question organizations have been asking in the wake of growing cyberattacks across industries. A growing number of data breaches have led to loss of customer data, disruptions in services, significant financial losses in addition to penalties and fines by regulatory bodies, loss of brand reputation, along with a host of other damaging outcomes. As cybersecurity and compliance experts, we decided to take a preventative approach and help businesses learn about the ways they can avoid a cyberattack from paralyzing their operations and damaging their revenue.
The risk of cyberattacks have not only been growing over the last decade, they have also been well documented as a global risk, not limited by geographical boundaries, the size of the business, or net worth of the individuals they impact. The Global Risks Report 2020 by the World Economic Forum placed cyberattacks on critical infrastructure as the top 5th global risk in 2020. On page 63 of the report, they also mention “Cybercrime-as-a-service is also a growing business model, as the increasing sophistication of tools on the Darknet makes malicious services more affordable and easily accessible for anyone.” While we continue to explore the role of AI in contributing to security threats and security tech, we are confident that organizations will triumph by using a variety of tools that can help them safeguard critical infrastructure, customer data, sensitive information, and business operations.
Consultants at databrackets have worked with a wide variety of organizations for over a decade and helped them test their systems to meet compliance requirements and security benchmarks. With our experience across security frameworks like ISO 27001, SOC 2, HIPAA, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC, 21 CFR Part 11 etc., we have created a list of investments in security tech to help you prepare for the Top 10 trends in 2023.
1) Creating a strong foundation for Cybersecurity
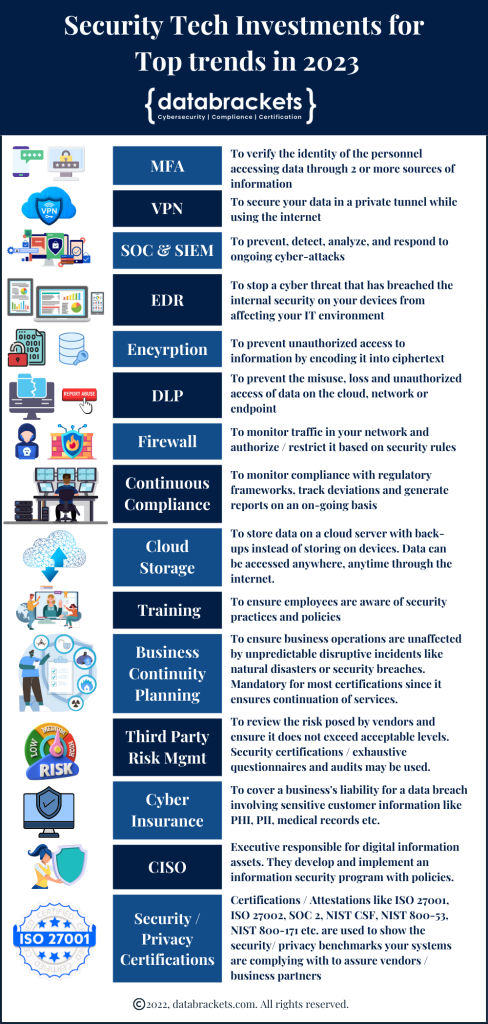
Data breaches are often linked to a weak foundation. As long as your system architecture, applications, and your access management is based on a strong foundation, the possibility of a data breach is minimized. Based on our experience, we strongly recommend that you consider some of the foundational technologies mentioned in the table below if you haven’t already implemented them.
Creating a strong foundation for cybersecurity | Security Tech | What is it? | Cost | Popular Brands | |
|---|---|---|---|---|---|
Multi Factor Authentication (MFA) | MFA helps you to verify the identity of the person accessing your data. It is an authentication system where a user is given access after providing 2 more pieces of evidence. An example of MFA is a Password / Pin along with a Code / OTP sent to your mobile number or an authenticator code generated in an app. Only a person who has both – a Password / Pin along with a Code/OTP, can login to your system and access data. This creates 2 barriers to reach data, ensuring that if even one is breached, the system protects the data from an unauthorized user. It is important to use password aging policies and regularly change the security questions in addition to MFA. Administrator accounts and personnel with access to a large amount of data and sensitive data / PII, must have MFA. | $$ | Microsoft Authenticator, Google Authenticator | ||
Virtual Private Network (VPN) | A Virtual Private Network (VPN) is used to create an encrypted connection between a device (computer, smartphone, tablet) and the internet. It encrypts your data and communication, keeps your identity hidden and allows you to send encrypted data through a private tunnel, even when you use a public network. This helps to prevent an attack called ‘Man in the middle (MITM) attack’. VPN is recommended for data being sent from remote locations to the cloud or on-prem site. | $$$ | Cisco AnyConnect VPN | ||
Security Operations Center (SOC) & Security Incident and Event Management (SIEM) | A Security Operations Center (SOC) and Security Incident and Event Management (SIEM) are strategies used to enhance cybersecurity by actively preventing a breach by monitoring network connections.
A SIEM allows you to collect and analyze log data from all your digital assets in one place. This helps you to recreate cyber incidents from the past and understand new ones to analyze the details of suspicious activity and strengthen your level of security. A SOC helps you to prevent, detect, scrutinize, and respond to ongoing cyber-attacks.
SIEM can help you detect a breach in a few hours as opposed to the usual time of several days, sometimes exceeding 100 days. SIEM services can be expensive because they are billed based on the log data generated. | $$$$ | Microsoft Azure Sentinel,
Sumo Logic
| ||
Endpoint Detection and Response (EDR) & Extended Detection and Response (XDR) | An endpoint detection and response system (EDR) is a set of tools used on your devices as a final barrier. It automatically detects threats that have breached your internal security and sends you an alert. An Extended detection and response (XDR) consolidate data from a variety of tools and extends the visibility, your ability to analyze and respond across devices / endpoints, networks, workloads and users.
These security technologies not only help you to detect an ongoing cyber threat but also to stop it before it affects your IT environment. They shorten the reaction time. | $$ | Sentinel One, CrowdStrike | ||
Encryption | Encryption software is used to conceal information from unauthorized personnel by translating it into a code. It uses digital keys and mathematical algorithms to encode data into ciphertext. Data can be decrypted only by authorized personnel who have the key. Encryption helps you maintain data privacy, confidentiality, integrity, and the authenticity of the source from where the data originated. | $$$ | AES 256,
AES 128,
TLS 1.3 | ||
Data Loss Prevention (DLP) | DLP consists of a set of tools and processes to prevent the misuse, loss, and unauthorized access of information. There are 3 types of DLP software: Endpoint, Cloud, and Network. They begin by classifying the data to identify what is confidential and critical to the business. Then it identifies violations of company policies for compliance benchmarks like HIPAA, GDPR, etc. It enforces remediation of vulnerabilities by sending alerts and ensuring encryption is implemented to avoid misuse of data. DLP protects data at rest and in motion in the cloud, network, and endpoint. | $$$$ | Proofpoint, Symantec,
Microsoft | ||
Firewall | A firewall is a network security device. It inspects the traffic to and from a network and authorizes or restricts it based on a set of security rules. There are different types of firewalls – packet-filtering firewalls, web application firewalls, next-gen firewalls, NAT firewalls and proxy firewalls. | $$$ | Palo Alto,
Cisco,
Checkpoint | ||
Cloud Storage | Cloud storage implies using ‘the cloud’ (multiple servers in a variety of secure locations) to store digital data instead of storing it on a device. This practice enables organizations to protect sensitive information more securely and ensure that it cannot be accessed, modified or deleted by unauthorized personnel. | $ | AWS,
One Drive, Google Drive | ||
These tools create a strong security foundation and minimize the potential for a data breach by increasing the barriers for entry.
2) Stronger cybersecurity regulations
With the increased complexity of cyberattacks, regulatory authorities are aware of compliant organizations whose security has been breached. This points to the need to enhance security benchmarks and we foresee tightening of regulations and compliance benchmarks. To keep up with this trend, we recommend implementing and strengthening your GRC Program with high visibility for stakeholders and management. This will help management to know the level of security they will be committing to customers when they sign contracts, and what they need to implement and comply with. An integrated governance, risk and compliance program will also take into account the law of the land across countries and states. While there may be overlaps between security regulations, identifying the key regulatory requirements, being able to conduct a comprehensive assessment, identifying the gaps, and having a remediation program will be critical.
3) Continuous Compliance & Security Monitoring
With the growing trend of cyberattacks infiltrating an organization’s systems from multiple sources, there is a need to constantly monitor all security controls and ensure they are functioning at optimal capacity. Attacks today are often disguised as legitimate emails, links, messages and data which can be very destructive once they enter your systems. Without tools to check the contents of every byte and security controls to monitor every aspect of your IT architecture, 24/7, it may be difficult to protect sensitive information and stay compliant with security benchmarks. This is even more vital for organizations with data in the cloud. You may lose revenue not just due to a cyberattack but also from fines, penalties, loss of brand reputation and termination of contracts. It is critical to prove that your systems were compliant with all the security controls promised to customers at the time of the attack. This is where continuous compliance platforms come in since they are automated and mapped to the controls of security frameworks.
Continuous compliance and security monitoring software is offered by a variety of GRC platforms. They map the controls of security and privacy frameworks like ISO 27001, SOC 2, HIPAA, GDPR, NIST etc. and link it to the various tools in your system. They monitor deviations and send alerts about possible loopholes that need to be patched and breaches. While organizations can use automated cloud monitoring tools offered by AWS Security Hub, Microsoft Sentinel etc., there is a need to expand your scope and review your risk management plan. An integrated GRC platform that is built to showcase your compliance with security and privacy frameworks goes beyond cloud monitoring tools and helps you review your risk management plan on a regular basis and maintain updated reports about how your controls are performing vis-à-vis what is expected. These reports become your evidence documents and help you with audits and customer requests.
4) Managing hybrid & remote work environments
Insider threat is one of the greatest risks to security as seasoned hackers come up with newer ways of targeting employees, vendors and consultants who work closely with sensitive data. This threat gets magnified in hybrid and remote work environments, which have become the new normal after the Covid-19 pandemic. Organizations can invest in information, training, and security tech to ensure a high level of security in this new normal. Some key investments are:
1. Review the BYOD Policy and Technology: While several organizations have pivoted in the pandemic by using BYOD policies to support employees working from home, this measure is fraught with security risks. Some ways to make it more secure are by enabling the IT team to use a secure enclave on the business network to separate the business data and customer data from non critical resources. Additions to the BYOD policy also need to cover MFA, increased security awareness training, encryption of devices, the use of firewall(s) managed by the organization, EDR and XDR, mandatory use of a VPN and Cloud Storage. Organizations can also add SIEM, SOC and DLP, to ensure that every device that accesses sensitive information has a benchmarked level of security.
2. Increase the frequency of Security Awareness Training: People have been found to be the weakest link in cybersecurity. Technology cannot alter it’s behavior since it functions as per it’s programming. However, people, specifically employees, vendors, suppliers, and anyone who has access to sensitive information, can behave differently depending on how well they are trained. This puts the onus on the companies to train their staff more frequently, evaluate them frequently to make sure they understand the intent of the training. Companies also need to identify the areas where training isn’t adequate and then retrain them to ensure they are sufficiently equipped to handle any kind of incidents. You also need to update the security awareness training at regular intervals to include new threats that are gaining momentum and prepare your team to prevent a security incident.
3. Create a strong foundation for cyber security on personal devices: Using security tech for off-site work, ensures that sensitive information is accessed and used with the same level of cyber hygiene, as if the staff were on-site. We recommend the following tools to effectively manage remote and hybrid work.
Multi Factor Authentication (MFA)
Cloud Storage
Firewall
Virtual Private Network (VPN)
Encryption of personal devices
Endpoint detection and response (EDR) and Extended Detection and Response (XDR)
These tools help to create a level playing field and allow work to be done from any location. Encryption helps the IT team to erase the data and take control of the data if the device is lost.
5) Business Continuity Planning (BCP)
In 2022, extreme weather led to18 disasters in the US including floods, droughts, storms, and wildfires. This cost the economy $165bn in damages. Of these, Hurricane Ian in Florida cost $112.9bn in damages. Apart from the severe economic loss, several thousand businesses were disrupted. The disruption in business operations has been growing since the start of the Covid-19 pandemic in March 2020, the continuation of natural disasters in 2020 and 2021 along with the growing number of ransomware attacks. This has reached unprecedented limits since it is no longer restricted to the geographical boundaries of some countries.
To cope with this new normal, organizations need to build resiliency in their infrastructure and invest in business continuity planning. The plan needs to include all 3 pillars – People, Process and Technology, which are perfectly aligned to respond during disruptions. They need to build in redundancy with support resources as well, to manage any shortfall. They also need to go beyond having a plan and invest in a series of back-ups that can be accessed securely when the disruption occurs. They need to test the plan, run simulations, and make sure it works. The transition from regular business operations to the back-ups systems needs to be seamless.
6) Cyber Insurance
Cyber Insurance, as an industry, has been growing exponentially. According to a report by Verizon, ransomware attacks have grown by 13% in 2022, which is more than in the last 5 years combined. Organizations have begun to accept that these targeted attacks are no longer aimed at specific industries or large organizations. SMBs are just as likely to be targeted as large enterprises. A data breach leads to a loss of revenue, loss of trust from customers and a negative impact on your brand reputation along with fines and penalties by regulatory authorities. Cyber Insurance has been a panacea to protect the organization’s bottom line from some of these.
We recommend organizations learn about the eligibility criteria to get cyber insurance and manage their infrastructure and controls to meet these guidelines. Having a strong foundation for Cyber Security with MFA, Access Management, Identity and Authentication controls, Encryption, Cloud Storage, VPN and Firewalls is the starting point. Organizations should also undergo a comprehensive Security Risk Assessment with a detailed Vulnerability Assessment and Penetration Testing. This helps to find the loopholes in your systems, so you can patch them before they are compromised. A positive report from such an analysis is usually one of the key documents that underwriters require for cyber insurance.
7) Vendor Security and Third-party Risk Management
Vendors, suppliers and third parties present a significant risk to an organization’s IT infrastructure. They have access to organizational data that needs to be regulated. One way to ensure that they meet high security benchmarks, is to ensure they have an ISO 27001 or SOC 2 Certification and to ensure their involvement is limited to secondary functions not the core business. Outsourcing can be efficient when it is managed, and security guidelines are made mandatory.
As part of a strong vendor management program, we recommend creating a list of all vendors and categorizing them based on their involvement in the business and access to data. Vendors who are categorized as high risk and medium risk should be monitored more closely, regularly audited and they should also be required to publish their security guidelines.
8) Implementing SOC & SIEM
A Security Operations Center (SOC) and Security Incident and Event Management (SIEM) are tools that help an organization create a strong foundation for cyber security and actively prevent a breach by monitoring network connections. A SIEM platform allows you to collect and analyze log data from all your digital assets in one place. This helps you to recreate cyber incidents from the past and understand new ones to analyze the details of suspicious activity and strengthen your level of security. A SOC helps you to prevent, detect, scrutinize, and respond to ongoing cyber-attacks.
They help you analyze logs in real time and identify a breach before it occurs. They offer the option of an automated response to deviations based on established security parameters. This goes beyond automated alerts and allows you to respond in time. SIEM can help you detect a breach in a few hours as opposed to the usual time of several days, sometimes exceeding 100 days.
SOC and SIEM, are not only becoming one of the must-haves for cyber security, one of the key arsenals in your toolkit against a hacking attempt, but also an integral part of regulatory compliance. Security frameworks have begun including them to ensure that cyber hygiene keeps up with the dynamic and complex nature of cyber-attacks today.
9) Hiring a CISO
A Chief Information Security Officer is primarily responsible for managing the data security, privacy, regulatory and compliance requirements in accordance with the state, federal and international laws, as applicable. Large enterprises usually have in-house intelligence to ensure their investment in security tech is based on best practices and their CISO is the strategic head for those decisions. SMBs can benefit from this strategic guidance and manage their investment in security tech effectively, by hiring a CISO on a part-time basis. While cloud providers have several security features built into their services, the entire landscape of business operations is vast and has many loopholes that need to be protected. Hiring a CISO is a move that not only assures customers, but also helps companies stay up to date on their security investments.
10) Getting a Security or Privacy Certification
Security and Privacy certifications are highly valued by customers, partners and potential investors. Organizations have begun asking for certifications like ISO 27001, SOC 2, NIST Cybersecurity Framework etc. in their RFPs and RFQs. It is becoming the norm since these benchmarks confirm the level of cyber hygiene their systems and data will be exposed to. These certifications also help you answer vendor questionnaires that run into hundreds of pages, since the final report has a detailed analysis performed by independent and authorized personnel. Reviewing the final report is easier for your customer than going through every response in a vendor management questionnaire. We recommend getting a Security or Privacy certification not just for the competitive edge they give you, but also for the guidance about the security tech you need and the planning involved in streamlining your processes and building resiliency in your business operations. While the initial cost of meeting these benchmarks is high, in the long run, they support revenue generation and result in a high return on investment.
Can databrackets help you with security tech investments?
Experts at databrackets have extensive experience in supporting organizations align their processes with security frameworks like ISO 27001, SOC 2, HIPAA, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC, 21 CFR Part 11 etc. We are constantly expanding our library of assessments and services to serve organizations across industries. If you would like to connect with an expert to better understand how we can customize our services to meet your specific requirements, do not hesitate to schedule a consultation.
Related Links:
Srini Kolathur
Srini is the Director of databrackets.com. He is a results-driven security and compliance professional with over 25 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are CMMC, SOC 2, ISO 27001, FedRAMP, NIST SP 800-171, NIST SP 800-53, NIST Cybersecurity Framework (CSF), HIPAA, Security Risk Assessments, among others. He is a Lead CCA for CMMC, CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE. He has verified all the technical information in this blog and co-authored it with Aditi Salhotra.