 CMMC is a security framework that is mandatory for contractors who want to work with the Department of Defense (DoD). It is based on the US National Institute of Standards and Technology (NIST) family of standards, specifically on NIST SP 800-171. It was first introduced as a 5-tiered framework in 2020. The next version of the framework, CMMC 2.0, is currently being finalized with a 3-tiered structure and several updates.
CMMC is a security framework that is mandatory for contractors who want to work with the Department of Defense (DoD). It is based on the US National Institute of Standards and Technology (NIST) family of standards, specifically on NIST SP 800-171. It was first introduced as a 5-tiered framework in 2020. The next version of the framework, CMMC 2.0, is currently being finalized with a 3-tiered structure and several updates.
Rulemaking for CMMC 2.0 is scheduled to be completed by the end 2023 and it is expected to be part of DoD contracts. Organizations are encouraged to complete the implementation process before the end of 2023, to ensure they can complete the certification process in time to bid for contracts, as this requirement is phased-in during FY 2024.
databrackets and Tego believe that DIB companies / Organizations seeking certification (OSCs) should be made aware of the CMMC implementation gaps, so they are able to avoid them. databrackets is enroute to becoming a CMMC Third Party Assessment Organization (C3PAO), that will conduct CMMC audits and issue the CMMC certificate. This blog is part of our collaborative effort with Tego, a Registered Practitioner Organization (RPO) committed to supporting organizations comply with CMMC 2.0 benchmarks and meet technological and process requirements. We have also jointly presented a webinar ‘Prepare for CMMC 2.0’ to help DIB companies plan their CMMC journey.
CMMC Compliance with an RPO
A Registered Practitioner Organization (RPO) offers consulting services to help you get ready for your CMMC Certification by a C3PAO. To avoid the implementation gaps that you may encounter, let us begin by discussing the CMMC compliance journey, when you work with an RPO.
1. Pre-assessment and Gap Analysis of your existing controls against CMMC requirements
2. Creating a Plan of Action & Milestones (POA&M) to identify the steps and technology you need to address the gaps
3. Cost-benefit analysis of a CMMC Certification
4. Implementation of new controls identified in the POA&M
5. An RPO can help with 1. through 4.
6. C3PAO Assessment and Certification
When you engage the right RPO, and undergo a thorough pre-assessment and gap analysis, you can identify and prioritize your gaps at the outset. This saves time and helps you create plans of action and milestones (POA&Ms) that will ensure you meet CMMC benchmarks. We recommend using the CMMC framework as a risk management tool and a best practice framework as well. Once you correctly identify the gaps and fix them, your RPO should be monitoring your progress and adjusting their assessment of your security posture. Once they confirm that you are ready, you can proceed with the assessment by a C3PAO and get certified.
NIST SP 800-171 Self-Assessment
Sometimes, companies begin their CMMC journey by conducting a self-assessment using NIST SP 800-171. Typically, the scoring is inaccurate and almost always over-favors the controls in their environment. Additionally, the self-assessment may be done by somebody that’s not there anymore or done by one person who hasn’t engaged multidisciplinary inputs that are required for understanding the control environment. An RPO can assess your environment more accurately because CMMC 2.0 includes additional security requirements that go beyond the scope of NIST 800-171. It is important to note that identifying what you’ve done so far to evaluate yourself is a huge step forward when you undergo a pre-assessment. This not only shows maturity but also helps them when they engage an RPO.
Cost of CMMC Implementation
The cost to implement CMMC 2.0 controls depends on the size and complexity of your organization. In general, the cost depends on the scope and the controls you need to implement. The cost of the report by the RPO depends on the scope and assets while the cost of the additional controls you need to implement will depend on your environment. The best way to manage the cost is to engage an RPO and analyze your specific environment to get an idea of what the cost will be. You need to make sure there’s a business case for it, particularly if you plan to comply with CMMC 2.0 Level 2. There needs to be a reckoning with your business model. During your pre-assessment, you need to identify if it’s worth continuing business in the DIB because it is going to be a substantial investment.
Engaging with a C3PAO
As you move through that POA&M process, if they have been written correctly, you will be able to estimate when you will meet your milestones and be ready to engage a C3PAO. You don’t have to have them completed before you engage the C3PAO. In fact, as you’re moving through the plans of action with still some open, it’s recommended that you try to engage the C3PAO without losing time. When the rulemaking is finished and CMMC certification becomes a requirement, there’s going to be a rush on getting appointments with a C3PAO. Working with a good RPO can help you manage your compliance process and get confident about meeting your milestones.
Time required to comply with CMMC
While the journey to becoming CMMC compliant seems extensive, the total time required depends on the organization and whether you are aiming for CMMC Level 1 or Level 2. The total time required also depends on the size of your organization, how complex your systems are and how much Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) you have in their environment. Some organizations only need to comply with Level 1 because they just have FCI. Others have CUI in very managed locations. Your RPO should be validating these elements and once you’re able to identify where your CUI is, you can estimate the time it would take your organization to comply with CMMC standards. Level 1 compliance may take 2-4 months and Level 2 may take longer since it has many more controls.
Top 5 Implementation Gaps for CMMC
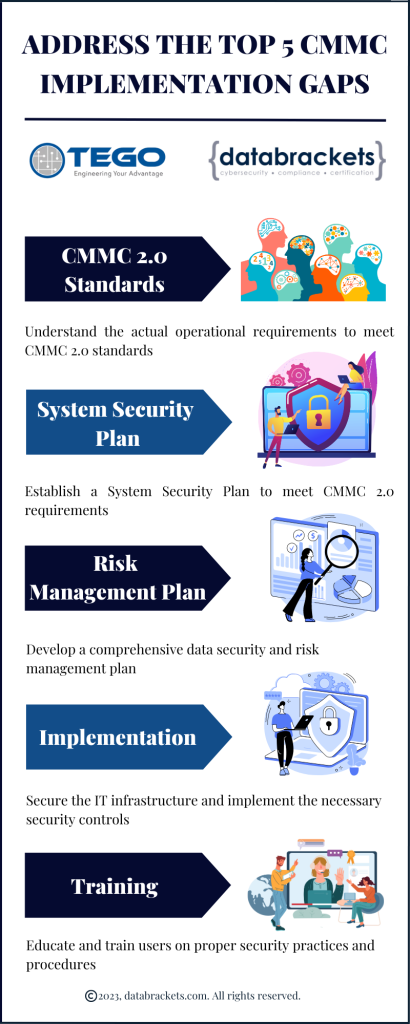
Understanding these nuances of the process, will help you understand the top five implementation gaps for CMMC
CMMC 2.0 Standards: Understanding the actual operational requirements to meet the CMMC standards.
System Security Plan: Establishing a suitable System Security Plan to meet CMMC compliance requirements.
Risk Management Plan: Developing a comprehensive data security and risk management plan.
Implementation: Securing the IT infrastructure and implementing the necessary security controls.
Training: Educating and training users on proper security practices and procedures.
Few organizations invest time and resources to understand their operations, track where CUI is and try to manage it. The key is in understanding how protected information moves through your environment. There are a lot of ways to do it. Tego interviews various stakeholders from the organization. A roundtable discussion of who’s using CUI is always the best place to start. This includes the person who did the NIST 800-171 scoring, HR, the Heads of the lines of business, etc. RPOs also employ various tools that help you identify and then mark the CUI in your environment over time. This is critical since protected information enters and exits your environment and you need to identify where it is in your CRM, in your unstructured data etc. Most of those tools also offer additional security that can complement control requirements in CMMC.
The next critical point is establishing a suitable System Security Plan. Some organizations use NIST 800-171 to complete a self-assessment, but they don’t really embrace the framework through which they want to manage their risk. The SSP is a comprehensive plan that outlines an organization’s approach to securing its systems and protecting its sensitive information. It is a key component of the CMMC assessment process and is required for all CMMC certification levels.
The SSP must be prepared and maintained by the organization seeking CMMC certification, and it must address all aspects of the organization’s security posture, including physical security, access controls, incident response, network security, and system configuration. The SSP must also include detailed information on the organization’s cybersecurity policies, procedures, and practices, as well as any third-party service providers used by the organization. The SSP addresses completeness and eliminates big gaps. For example, if you have a network administrator do the NIST 800-171 score without complete awareness of where CUI was, which is the number one gap, you end up having organizations that lack actual alignment with NIST 800-171. We have seen a lot of things on paper where the organization hasn’t really embraced the comprehensive data security and risk management plan. Within those controls, are actions that you need to take and things you need to do. Organizations who want to be CMMC compliant, need to run a secure organization based on that framework.
Organizations also tend to have compliance gaps because of budgeting. Complying with NIST 800-171 and CMMC is an opportunity for organizations to refresh their security infrastructure. We have seen some neglect in this area with regard to investment in tools. Organizations need to take the time to invest in this critical update. We have had tough conversations about the cost because it can become very expensive. Planning to work with the DoD forces organizations into making an investment in their security infrastructure, to become CMMC compliant.
Lastly, educating and training security users or training users in security practice is important. Users are always the number one risk in any organization, in any context. We have seen this being neglected or lacking in organizations. Training needs to go beyond just doing phishing campaigns and an annual security awareness training.
We would also like to mention that some organizations will endeavor to manage CMMC compliance over time. While, it is still recommended to maintain a relationship with your RPO in an advisory context, some organizations may want to manage day-to-day compliance with internal staff. In that case, it is recommended they get some staff members CCP Certified. Organizations can get that training through our partners. In addition to that, there are some things that may not require a CCP from the operation side where you want individuals such as a network admin to be schooled on the specific requirements that you need for network security, and we can also offer those trainings as pursuant to the requirements in CMMC.
Without having CMMC compliance, you will ultimately be precluded from participating in contracts as a subcontractor or prime in the DIB. So, you’re going to have to invest your time and resources in the requirements if there’s a business case for it and embrace the fact that there’s going to be money spent. Aside from the risk of losing DoD contracts, this is a best practice framework. Alignment to it and following CMMC certification standards reduces risk in your environment too. So, there are more benefits to comply with it, apart from the revenue that could come from a DoD contract.
Engaging with an RPO for your certification efforts is recommended because the RPO has invested the time and energy to understand the specifics of CMMC and its requirements. Doing that pre-assessment gap analysis is the way to prioritize what you need to do both for certification and for risk reduction. As an RPO, Tego offers technical mitigations, which they are suited for because they are an IT professional services organization, capable of helping with a security infrastructure refresh. They’re also available to help implement controls such as network segmentation, the hardware upgrades, server OS upgrades. They extend their support with all of these under the management of the CMMC Registered Practitioners (RPs) that are on staff at Tego.
How databrackets can help you with your CMMC Journey
databrackets is an authorized C3PAO and independent consulting organization for CMMC. We offer Certification OR Readiness and Consulting services for CMMC. To avoid a conflict of interest and abide by CMMC’s independence requirements, we do not offer both services to the same client.
We are an ideal partner for either service since we bring over 15 years of proven expertise in helping organizations achieve compliance or certification with the most rigorous cybersecurity and data privacy standards, including ISO 27001, SOC 2, HIPAA, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, and CMMC. We are an authorized certifying body for ISO 27001 and 3PAO for FedRAMP.
Schedule a Consultation to work with us as your C3PAO for CMMC Certification or as your Compliance Partner to help you prepare for it.
A. Why Choose databrackets as your C3PAO
1. Proven Multi-Framework Expertise
What makes databrackets particularly valuable is our extensive experience across complementary frameworks, including NIST SP 800-171, NIST SP 800-53, SOC 2, ISO 27001, HIPAA, and NIST Cybersecurity Framework. We are also an authorized certifying body for ISO 27001 and 3PAO for FedRAMP.
This breadth of knowledge enables our assessment teams to understand how CMMC controls integrate with your existing compliance efforts and identify synergies that strengthen your overall security posture.
2. Technical Environment Proficiency
databrackets’ assessment team of CCAs and CCPs has the specialized technical competence essential for accurate CMMC evaluations. Our experience spans diverse technological environments, from traditional on-premises infrastructures to complex cloud deployments, ensuring we can effectively assess whatever technical landscape your organization operates in.
3. Strategic Timeline Management
With proven capability in managing sophisticated assessments spanning the typical 4–8-week timeframe, databrackets understands how to minimize disruption to your operations while ensuring comprehensive evaluation of all 110 NIST SP 800-171 security controls.
As a authorized C3PAO with extensive cybersecurity and compliance experience, databrackets offers a deep understanding of the CMMC assessment process. This comprehensive expertise enables us to conduct thorough assessments with clear explanations of findings and methodologies, resulting in more insightful evaluations for organizations seeking certification.
To inquire about our C3PAO Services, contact our team at sales@databrackets.com or schedule a free consultation.
B. Why Choose databrackets for Your CMMC Compliance Journey
We specialize in transforming CMMC compliance from a daunting obstacle into a strategic business enabler.
Proven Track Record: Over 15 years supporting organizations across diverse industries with complex compliance requirements
Comprehensive Approach: End-to-end support from initial assessment through ongoing compliance
Industry Recognition: Authorized certifying body for ISO 27001 and 3PAO for FedRAMP
Strategic Partnership: We don’t just help you achieve compliance—we help you leverage it for competitive advantage.
Our Comprehensive CMMC Compliance Services include:
1. Strategic Planning & Assessment:
CMMC readiness assessments and comprehensive gap analysis
CUI system boundary definition and scoping guidance
Network architecture documentation and CUI flow diagrams
Risk assessment and vendor compliance evaluations
2. Implementation & Documentation Support:
System Security Plan (SSP) development and customization
Complete policy and procedure documentation suite
FIPS validation documentation and shared control matrices
Evidence collection strategies and management systems
3. Assessment Preparation:
Mock assessments and readiness validation
CMMC documentation optimization and organization
Personnel training and assessment preparation
C3PAO coordination and selection support
4. Ongoing Compliance:
Continuous monitoring and compliance maintenance
Annual affirmation support and triennial assessment preparation
Change management and configuration control guidance
Customized CUI awareness training programs
Schedule a Consultation to understand how we can customize our services to meet your specific CMMC requirements and timeline.
About databrackets
Our team of security experts has successfully supported organizations across a wide variety of industries in aligning their processes with critical security frameworks. We are an authorized certifying body for ISO 27001 and a 3PAO for FedRAMP.
We constantly expand our library of assessments and services to serve organizations across industries, maintaining partnerships to help clients prepare for and obtain critical security certifications.
For immediate assistance with your CMMC compliance journey, contact our certified experts at sales@databrackets.com or schedule a free consultation.
Helpful Resources:
Srini Kolathur
Srini is the Director of databrackets.com. He is a results-driven security and compliance professional with over 25 years of experience supporting, leading, and managing global IT security, compliance, support, and risk assessment in fortune 100 companies. Some of his key areas of focus are CMMC, SOC 2, ISO 27001, FedRAMP, NIST SP 800-171, NIST SP 800-53, NIST Cybersecurity Framework (CSF), HIPAA, Security Risk Assessments, among others. He is a Lead CCA for CMMC, CISSP, CISA, CISM, MBA. He is active in several community groups including Rotary International and TiE. He has verified all the technical information in this blog and co-authored it with Aditi Salhotra.