Over the last decade, service organizations have been asked to prove their level of cyber hygiene before they are awarded a contract. The RFQs and contracts of small-medium sized businesses, particularly SaaS providers typically include an annual Vendor Security Questionnaire, which is extensive and time-consuming. To save time, optimize costs and streamline resources, many SaaS providers have been opting to undergo a SOC 2 Examination and prove their compliance with industry-preferred Trust Services Criteria and security controls. This single report serves as proof since it is given by an independent and authorized CPA after their controls have been tested and it serves as an alternative to the Vendor Security Questionnaire. This blog is intended to help you compare a SOC 2 Report and a Vendor Security Questionnaire and decide which option works for you.
Comparing a SOC 2 Report and
a Vendor Security Questionnaire
A SOC 2 (Service Organization Control 2) report and a Vendor Security Questionnaire have some overlaps in terms of the controls they refer to. However, for some customers, they are not interchangeable. Here’s a brief overview of each:
SOC 2 Report
A SOC 2 report is an assessment of an organization’s controls related to security, availability, processing integrity, confidentiality, and privacy.
SOC 2 reports are conducted by independent third-party auditors and are designed to provide assurance to customers and partners about the security and privacy practices of a service provider.
SOC 2 reports provide detailed information about the controls and processes in place, along with an auditor’s opinion on their effectiveness.
These reports are often requested by customers to assess a vendor’s security and compliance posture.
Vendor Security Assessment Questionnaire
These are typically questions answered by vendors to their customers or partners. The number of questions can vary between 30 to 300, contingent upon the vendor’s risk profile.
Vendor security questionnaires are used to gather information about a vendor’s security practices, policies, and controls.
They may be customized by the customer to align with their specific security requirements and concerns.
These documents help customers assess a vendor’s security readiness, but they are based on self-reported information provided by the vendor.
In most cases, a SOC 2 report provides more comprehensive and independent assurance about a vendor’s security practices compared to a vendor security questionnaire. However, some organizations may still require vendors to complete their own security questionnaires or submit a SOC 2 Report and provide additional documentation to address specific security concerns or requirements.
How a SOC 2 Report streamlines
the Vendor Assessment Process
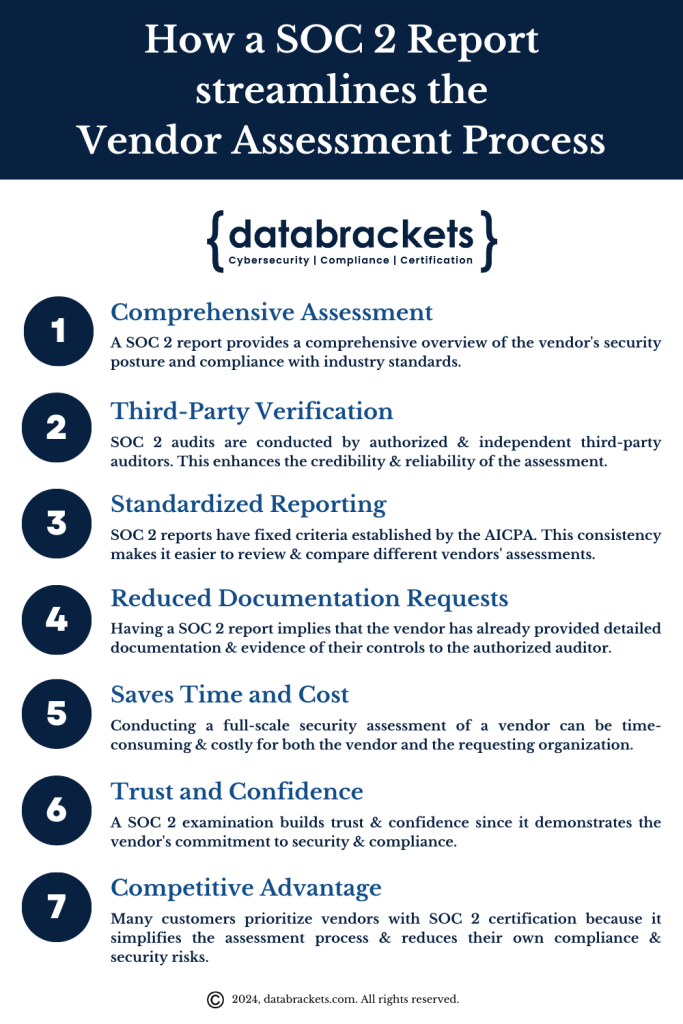
B2B Contracts & RFQs rely on a SOC 2 Report because it can streamline their vendor assessment process in several ways. Here’s how a SOC 2 report can achieve this:
1. Comprehensive Assessment: A SOC 2 audit involves a thorough examination of an organization’s controls and processes related to security, availability, processing integrity, confidentiality, and privacy. The resulting report provides a comprehensive overview of the vendor’s security posture and compliance with industry standards.
2. Third-Party Verification: SOC 2 audits are conducted by authorized and independent third-party auditors, which enhances the credibility and reliability of the assessment. The fact that an impartial auditor has validated the vendor’s controls can reduce the need for the requesting organization to conduct its own extensive assessments.
3. Standardized Reporting: SOC 2 reports follow a standardized format with fixed criteria established by the American Institute of Certified Public Accountants (AICPA). This consistency makes it easier for the requesting organization to review and compare different vendors’ assessments, as they are presented in a comparable format.
4. Reduced Documentation Requests: Having a SOC 2 report implies that the vendor has already provided detailed documentation and evidence of its controls to the auditor. When requesting a SOC 2 report, the requesting organization can typically access this documentation, reducing the need for additional, redundant requests for the same information.
5. Saves Time and Cost: Conducting a full-scale security assessment of a vendor can be time-consuming and costly for both the vendor and the requesting organization. A SOC 2 report can expedite the assessment process, saving time and resources for both parties.
6. Trust and Confidence: A SOC 2 examination builds trust and confidence among customers and partners. It demonstrates the vendor’s commitment to security and compliance, which can lead to more successful and long-lasting business relationships.
7. Competitive Advantage: Having a SOC 2 report can give vendors a competitive advantage. Many customers prioritize vendors with SOC 2 certification because it simplifies the assessment process and reduces their own compliance and security risks.
While a SOC 2 report can streamline the vendor assessment process, it’s important to note that it may not completely eliminate the need for additional assessments or specific requirements tailored to the requesting organization’s needs. The level of scrutiny and specific requirements can still vary based on the nature of the vendor relationship and the sensitivity of the data or services involved. However, having a SOC 2 report as a foundation can significantly simplify and expedite the assessment process.
Our Client Experience
We have numerous clients who have shared that they have had to dedicate considerable amounts of time to complete a range of vendor assessment questionnaires for their customers in regulated sectors. Their experienced security analysts or consultants from our team have dedicated 10-30 hours for each questionnaire and submitted an average of 10-20 questionnaires annually. However, strategic acquisition of third-party reports such as SOC 2 has allowed our clients to completely bypass this time-consuming process, thereby freeing up their schedule to focus on business-critical tasks. By being able to prove their commitment to security and privacy of data using a standardized format, they have been able to retain their customers and meet the requirement for documentation & evidence.
Key Takeaways
A SOC 2 report provides a standardized, independent assessment that offers broader assurance than ad hoc vendor security questionnaires, which often vary widely in depth, quality, and interpretation.
Relying on questionnaires alone creates inefficiency and inconsistency, as vendors must repeatedly answer similar questions while customers struggle to compare responses across different formats.
A SOC 2 report shifts the burden of validation from self-attestation to auditor evaluation, increasing confidence that controls are not only described but actually tested.
Questionnaires typically capture intent at a point in time, whereas a SOC 2 report—especially Type II—demonstrates how controls operate over an extended period.
Using SOC 2 reports streamlines vendor risk management by reducing repetitive due diligence efforts and enabling faster, more informed trust decisions.
SOC 2 does not eliminate the need for all follow-up questions, but it significantly narrows them by addressing common security concerns in a single, authoritative document.
The report’s scope is critical, as its usefulness depends on whether the assessed systems and trust criteria align with the customer’s reliance on the service.
Complementary user entity controls clarify shared responsibilities, highlighting areas where customer practices still influence overall risk.
Adopting SOC 2 as a primary assurance mechanism benefits both vendors and customers by improving transparency, consistency, and efficiency in security evaluations.
How databrackets can help you
with a Vendor Security Questionnaire
Our team of security experts conducts a thorough security assessment of your environment to understand your security controls, tools, techniques, processes & procedures. After this analysis, our customers can outsource the entire exercise of filling up Vendor Security Questionnaires to our team, as and when required. This has resulted in saving them an average of 400 hours of effort or 3-4 months, on an annual basis. Our team also engages with their customers on a need by need basis, to ensure they are fully supported in this endeavor.
A SOC 2 Examination takes a much shorter amount of time compared to repetitive filling of Vendor Security Questionnaires. Based on our recommendation, several clients have undergone a SOC 2 Readiness Assessment with our experts followed by their SOC 2 Audit by an authorized CPA. Our SOC 2 package has helped them to present their evidence and company information in a streamlined manner through dbACE, our GRC Platform. Through this optimized process, they have saved precious time & money.
While we recommend a SOC 2 Examination compared to an annual average of 400 hours of effort and time spent in repetitive filling of Vendor Security Questionnaires, we would also like to share that all SOC 2 Reports are not the same. A SOC 2 report provides detailed information about your security controls and processes, along with your auditor’s opinion of their effectiveness. The clarity and depth of your SOC 2 report depends on the expertise and reputation of the organization that has helped you prepare for your SOC 2 Audit and properly presented the evidence of how effective your controls are. When your evidence is presented with depth and accuracy, your auditor is able to gain a better understanding and evaluate your documentation. This clarity and depth impacts their opinion and subsequently your SOC 2 Report.
Additionally, the quality of testing varies between SOC 2 Auditors. Some auditors go in-depth and this thorough evaluation discovers issues that you may not be aware of otherwise. This helps you to identify the risk and implement measures to help your organization.
Hence, to have a SOC 2 Report that truly reflects your commitment to security and privacy, and which you can submit instead of a Vendor Security Questionnaire, you need to invest time and resources in the readiness process & work with a SOC 2 auditor who prioritizes a thorough evaluation.
How databrackets can help you with a
SOC 2 Readiness & Examination
databrackets works in conjunction with certified CPA firms to prepare our customers to get ready for a SOC 2 Examination and obtain a SOC 2 report. Some of the services by our security experts are:
Readiness Assessment & Recommendations
Testing of Controls, Vulnerability Assessment and Security Risk Assessment
Support to draft the Management Assertion for your SOC 2 Report
SOC 2 Examination by a certified CPA includes
Selecting the Trust Services Criteria
Finalizing the SOC 2 Audit Period
Scoping of the systems and applications
Sampling & reviewing the evidence and policies & procedures
Interviewing process owners
Analyzing the results
Documenting & reporting
The CPA that you chose to work with can access all your evidence in a streamlined manner on dbACE – our GRC Platform.
Overview of databrackets
Our team of security experts has supported organizations across a wide variety of industries to align their processes with security frameworks like HIPAA, 21 CFR Part 11, ISO 27001:2022, SOC 2, NIST SP 800-53, NIST Cybersecurity Framework, NIST SP 800-171, GDPR, CMMC etc.
We are constantly expanding our library of assessments and services to serve organizations across industries. Schedule a Consultation if you would like to Connect with an Expert to understand how we can customize our services to meet your specific requirements.
Summary
To summarize,
Vendor security questionnaires are commonly used to assess third-party risk, but their lack of standardization often leads to inconsistent, incomplete, and difficult-to-compare responses.
A SOC 2 report offers a more reliable alternative by providing an independent evaluation of controls against established trust services criteria, reducing reliance on self-reported security claims.
Questionnaires tend to capture stated intentions at a single point in time, while SOC 2 reports, particularly Type II, demonstrate how controls actually operate over an extended period.
The value of a SOC 2 report depends heavily on its scope, requiring customers to confirm that the assessed systems and criteria align with how they use and rely on the service.
Using SOC 2 reports can significantly reduce the operational burden on vendors by minimizing repetitive questionnaire responses and streamlining customer due diligence.
SOC 2 does not replace all customer inquiries, but it consolidates the most critical security information into a single, authoritative artifact that supports more focused follow-up.
Complementary user entity controls reinforce that risk management is shared, clarifying which responsibilities remain with the customer even when a SOC 2 report is provided.
Adopting SOC 2 as a primary assurance mechanism improves efficiency, transparency, and trust for both vendors and customers in the vendor risk management process.